Takeaways
- Mental models (how to decide) are necessary for effective Cyber Security (not just what to buy or how to implement).
- Cyber Security without strategies is sub-optimal (I will explain with a Sun Tze Art of War strategem 謀攻).
- Attack Surface management is a priority & something within your control because it will make you look at things from both perspectives: Offense & Defense.
Mental Models: Why they matter?
🧠 A mental model is simply a representation of how something works. We cannot keep all the details of the world in our brains, so we use models to simplify the complex into understandable and organizable chunks. - https://fs.blog/mental-models/
What is Cyber Defense? How is it different from Cyber Security? Cyber Defense is about the strategy (of what matters & why) employed to disrupt attacks, while Cyber Security focuses on how (tactically) to protect your network from threats. Strategies & Tactics are two sides of the same coin. Let’s dissect Cyber Defense with a First Principle mentality.
A Sure Route to Defeat…
🔥 Strategy without tactics is the slowest route to victory. Tactics without strategy is the noise before defeat - Sun Tze
There is no shortage of models & guides related to “HOW” you should implement products, controls & compliance with checklists. For instance, NIST’s “Identify, Protect, Detect, Respond & Recover” functions, controls for “Authentication, Authorization & Accounting”, Information Security requirements of “Confidentiality, Integrity & Availability”.
From Attack by Stratagem (謀攻) chapter:
🧠 故曰:知彼知己,百戰不殆;不知彼而知己,一勝一負;不知彼,不知己,每戰必敗。
Translates (by Lionel Giles) to:
📢 Hence the saying: If you know the enemy and know yourself, you need not fear the result of a hundred battles. If you know yourself but not the enemy, for every victory gained, you will also suffer a defeat. If you know neither the enemy nor yourself, you will succumb in every battle.
Most high-level frameworks & controls help with “knowing yourself” (indirectly) in terms of networks & assets. Many companies (& even government agencies) appeared in headlines for the wrong reasons related to breaches are pretty well-equipped with compliance checklists & controls.
Mistranslation of this stratagem assumes “victory when we know our enemy & ourselves”, which it is never the case for Cyber Defense since most organisations do not retaliate. We can at best work to remain “undefeated”, which is what “不殆” means. Unenviable job because no one remembers defenders’ “victories”, but everyone remembers the breaches.
Sadly, many are in the category of “know neither the enemy nor themselves”. They have poor network visibility & situation awareness that attackers can literally take their own sweet time to explore the victim’s network.
With these in mind, let’s examine the problem at its roots.
First Thing First: Necessary & Sufficient Conditions
Fire fighters & law enforcers don’t start off learning about fire engines, water pumps, patrol cars & fire-arms. Instead, every FireFighter needs to internalise the Combustion Triangle & for Law Enforcers, they learn Motivation, Means & Opportunity when evaluating suspects. So why should Cyber Defenders start off with assuming “prescriptions of HOW to …” (largely in form of buying products & ticking checkboxes) would assure safety & security?
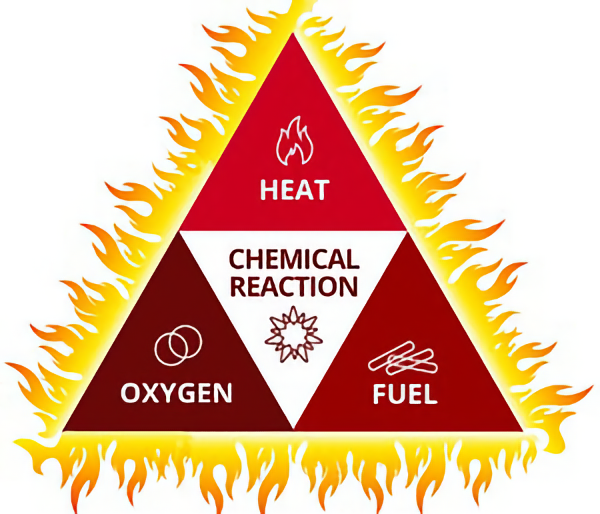
Combustion Triangle
Oxygen cut…
For (most) fire to burn, we need three ingredients to start a fire. Some may argue that exceptions like phosphorus self-ignites at room temperature without the application of heat, but that’s just initial reaction, to sustain any combustion, these 3 ingredients are still necessary.
Similarly, offenders (Threat Actors) have the Motive (for most cases, other than insanity), Means & Opportunity (Routine Activity Theory - Cohen & Felson, 1979) to act on victims (you & your networks).
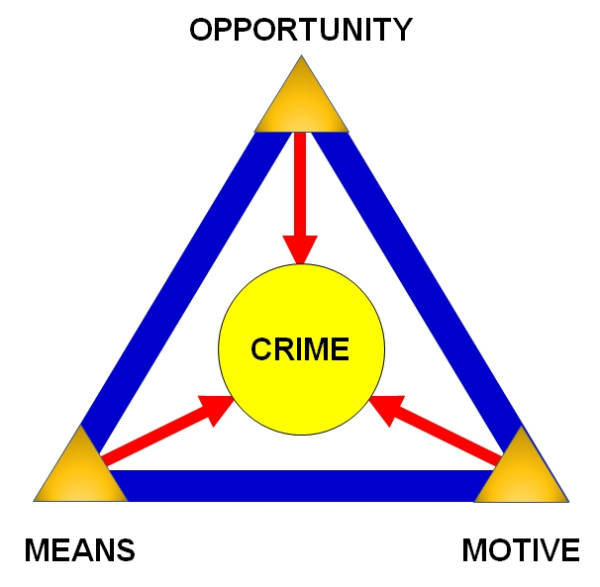

Opportunity denied…
Giving criminals an opportunity to snatch your valuables turns out to be a lot like oxygen for fire to burn. So what’s the equivalent for Cyber Attacks?
The Three-Tenets of Cyber Security
Three tenets for secure cyber-physical system design and assessment are a threat-driven quantitative mathematical framework for secure cyber-physical system design and assessment. This empirical approach has been used by the US Air Force Research Laboratory (AFRL) for secure system research and development. The Tenets were first documented in 2005 as a teachable methodology.
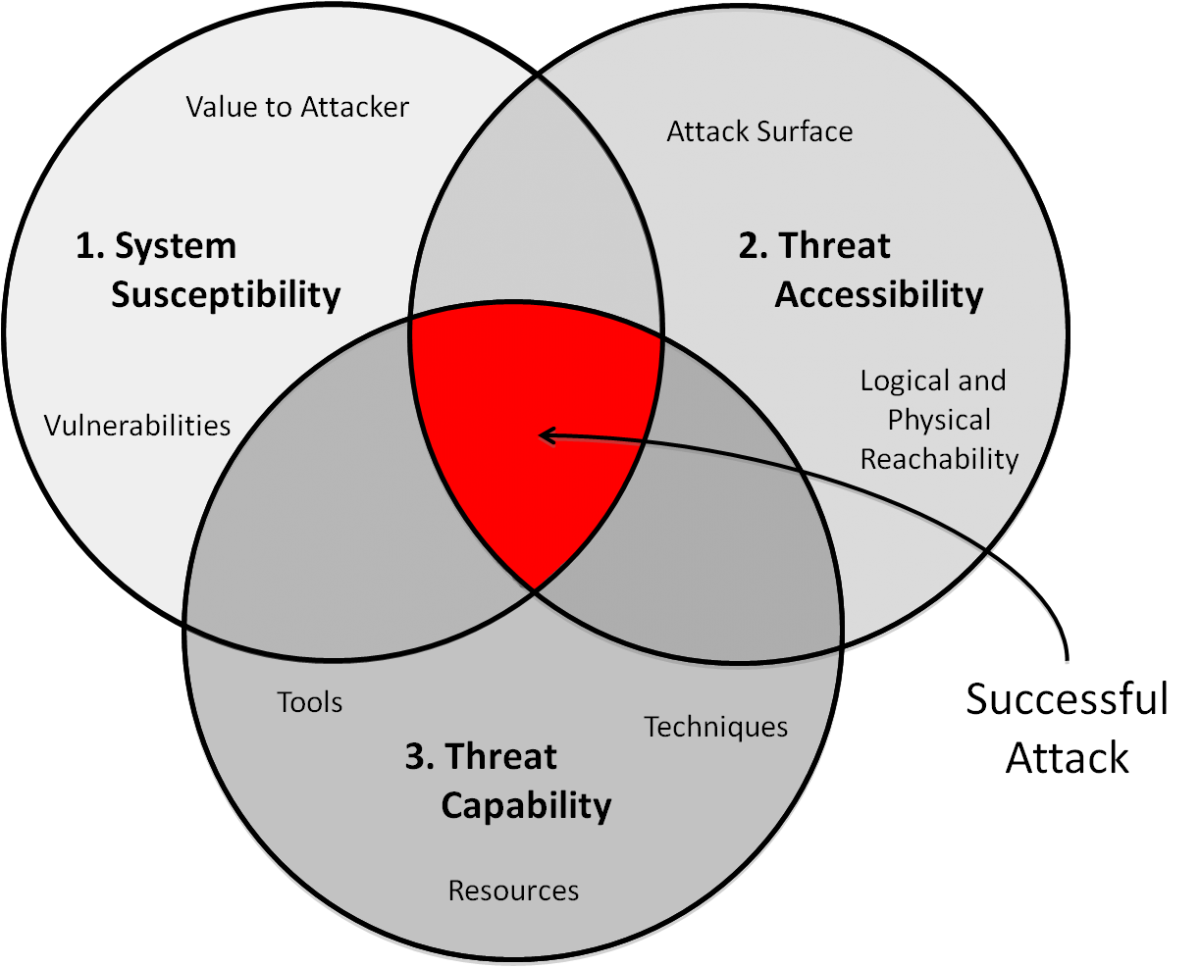
The Three Tenets threat model posits that three ingredients are necessary and sufficient for cyber-physical vulnerabilities to exist: i) system susceptibility, ii) threat accessibility, and iii) threat capability. Just like fires & crimes, all ingredients need to be present.
🔰 Fortunately, like the earlier animations, we can avert problems by removing or disrupting one or more of the conditions.
- A system is susceptible when it has value (to attackers) & vulnerabilities (exploitable by attackers).
- Attackers need access to know about system susceptibilities, thus accessibility to the system’s Attack Surface, which is the sum of access points to deliver attacks, either physically or logically.
- Even with access & knowledge, Threat Actors must possess the capabilities (to exploit) in terms of tools, techniques & resources in order to succeed.
What’s the “Oxygen” for Cyber Attacks?
Strategy #1: cutting off “oxygen” denies opportunities for attackers. So which of the three tenets is the “oxygen” & why (next section)?
| Fires | Crimes | Cyber Attacks |
|---|
| Fuel |
| (prices are high now) | Motives | System Susceptibility |
| Heat | Means | Threat Capability |
| Oxygen | Opportunity | Threat Accessibility |
Cyber attacks are prevalent simply because all three ingredients are always present. Threat Accessibility is the only condition that we can fully control because:
- Most systems, regardless of custom-built or bought off-the-shelve or cloud, are flawed or poorly designed & implemented (related to System Susceptibility).
- Legacy controls & mindsets (or ignorance) persist (related to System Susceptibility).
- Adversaries have the advantage of freely available offensive tools & knowledge but it is costly to monitor & defend (related to Threat Capability).
- Attackers just have to get it right once while defenders have to get it right always (infinite game) (related to Threat Capability).
The above are unfortunate (non-exhaustive) facts to live with, BUT we can choose HOW we expose our assets to networks.
Why Threat Accessibility is “Oxygen”?
To put the first mental model (i.e. the attack conditions) to practice & experience why Threat Accessibility is the “oxygen”. Most of my interns get bored just reading the 3-tenets paper. So to spice it up for them, I designed this first practical on Attack Surface management (check out YJ’s Intern notes):
- Sign up free cloud Virtual Machines running Linux with SSH (remote access) service & ZeroTier Virtual Private Network (this is NOT a sponsored post & ZeroTier is more of a Software-Defined Overlay for micro-segmentation than traditional VPN which is a gate-to-whole-internal-network).
- Learn which log & events to look at to observe persistent brute-force SSH authentication attempts (Threat Capability) immediately after starting the VM instance (before joining VPN).
- Shut off SSH service quickly to join VPN (a private network that consists of their laptops & the server VM).
- Realise despite poor password (system susceptibility), a simple configuration limits the service to only accept connections from within the private network, thus denies all brute-force attempts (just like the earlier fire blanket demo, server log no longer shows any new events after the configuration).
This exercise does not imply VPN services are the silver bullet & systems will become impenetrable, or we can be lazy with basic hygiene & condone weak authentication. But the odds of remaining “undefeated” is much BETTER when you manage Attack Surface as a priority because:
- It is often quickest, least effort & impact, especially for administrative services (privileged access thus high-value targets);
- It buys you time to prioritise your patching, starting from assets that are directly exposed, to the next hop & so on. As oppose to the naïve approach of “crown jewels” (first because your spreadsheet says so) that are far away from the initial pivot & often high impact when patching screws up;
- Attackers think in terms of connected-graphs & not a list with arbitrary sorting (yes, those silly “risk” formulas in your spreadsheets) based on opinions or preferences!
Three Tenets vs Art of War Stratagem
So let’s conclude this first part of three by relating the necessary & sufficient conditions with Attack Stratagem:
| Attack Conditions | Know yourself | Know your enemies | Examples |
|---|
| System Susceptibility | ✅ | ❌ | Keeping up with system patches |
| (needs to be done, but not enough because abusing system features is also a prevalent tactic to evade controls & detection) |
| Threat Capabilities | ❌ | ✅ | Subscribe to Threat “Intel” stories |
| (there are better ways to spend your budget) |
| Threat Accessibility | ✅ | ✅ | Executing Attack Surface & Vulnerability Management plans that make sense for your use-cases, networks & budget |
What’s Next?
Attackers tend to RINSE & repeat:
- Reconnaissance (gather information)
- Infiltrate
Networks (aka Initial Access)
- Spread (within networks aka Lateral Movement)
- Execute Objectives (that impact Safety of Cyber-Physical Systems; Confidentiality, Integrity & Availability of Information-Systems)
Attackers tend to RINSE (mnemonic) & repeat around the necessary & sufficient attack conditions.
—
Want to learn more? Check out https://www.jym.sg/cyber-security-in-7-weeks