###1: critical idor allow the attacker to get the access of any one server
An Insecure Direct Object Reference (IDOR) vulnerability was identified in the domain.com
remote server management feature, where the application allows authenticated users to connect and manage computers remotely.
The application exposes a client-controlled parameter, server_ids, which is used to associate users with specific servers for remote access and management. Due to missing server-side authorization checks, this parameter can be tampered with by an authenticated attacker to reference arbitrary server IDs belonging to other tenants or users.
By modifying the server_ids value in the request, an attacker can add their own user account to victim servers without permission. Once added, the attacker gains administrative/management access, enabling them to remotely connect to the victim’s computer and perform privileged actions.
This results in a complete compromise of targeted server resources, including unauthorized remote access, configuration changes, service control, data exposure, and potential lateral movement within the victim’s infrastructure.
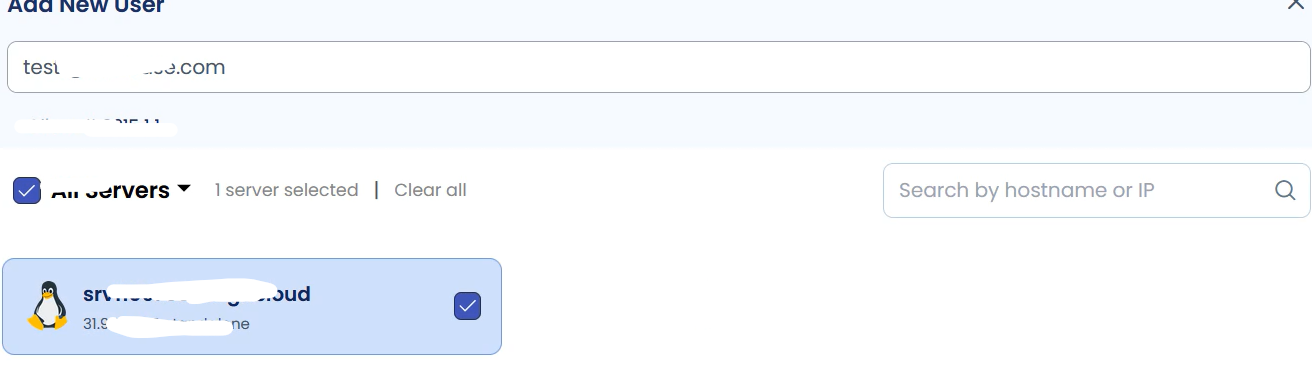
Step 1:
Login to the application using an attacker (low-privilege) account.
Step 2:
Intercept the request that adds a user to a server (e.g., when adding a user to your server) using a proxy tool (Burp, ZAP).
Step 3:
Locate the server_ids field in the JSON body and replace the legitimate server id with the victim’s server id (or ids).
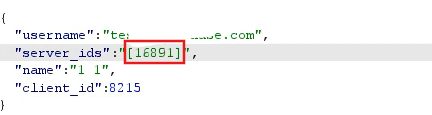
Step 4:
Forward the modified request. The attacker’s user is added to the victim server and can manage it.


Impact
Full account takeover of targeted servers — attacker user can manage, modify, or delete server resources.
Confidentiality / Integrity / Availability at severe risk for affected servers.
Lateral movement within the infrastructure if server credentials / integrations are accessible.
Business impact: Critical — direct compromise of customer systems and data, regulatory and reputational risk