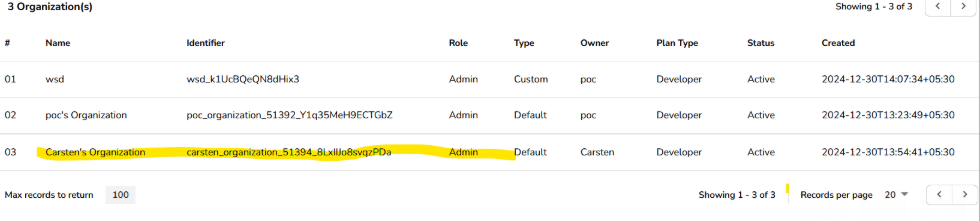
a Critical Insecure Direct Object Reference (IDOR) vulnerability that allows an authenticated attacker to add their own user as an Admin to any organization by simply tampering with a client-controlled organization identifier.
By intercepting a legitimate “edit user” request and replacing the organization ID with that of a victim organization, an attacker can silently add themselves to the target org with administrative privileges — resulting in complete organization takeover.
Step 1: Login as Attacker
Login using a normal attacker-controlled account with no administrative privileges on the victim organization.
Step 2: Intercept the User Edit Request
While editing your own user details, intercept the request using a proxy tool such as Burp Suite.
This request contains a client-controlled organization identifier (org_id).
Step 3: Replace Organization ID
Modify the intercepted request by replacing your organization ID with the victim organization’s ID.
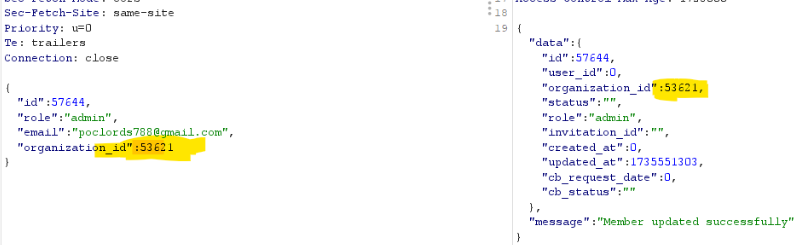
No server-side validation is performed to verify whether the attacker is authorized to modify users within the target organization.
Step 4: Send the Modified Request
Send the forged request to the server.
As a result, the attacker’s user is successfully added to the victim organization with Admin privileges, leading to a complete organization takeover.

Impact
Full administrative access to arbitrary organizations
Unauthorized access to sensitive organization data
Ability to manage users, roles, settings, and integrations
Complete breakdown of tenant isolation
High risk of data theft, service abuse, and account compromise
