Most developers obsess over SQL injection, XSS, and authentication bypasses.
Very few think about the Host header.
And that’s exactly why it becomes dangerous.
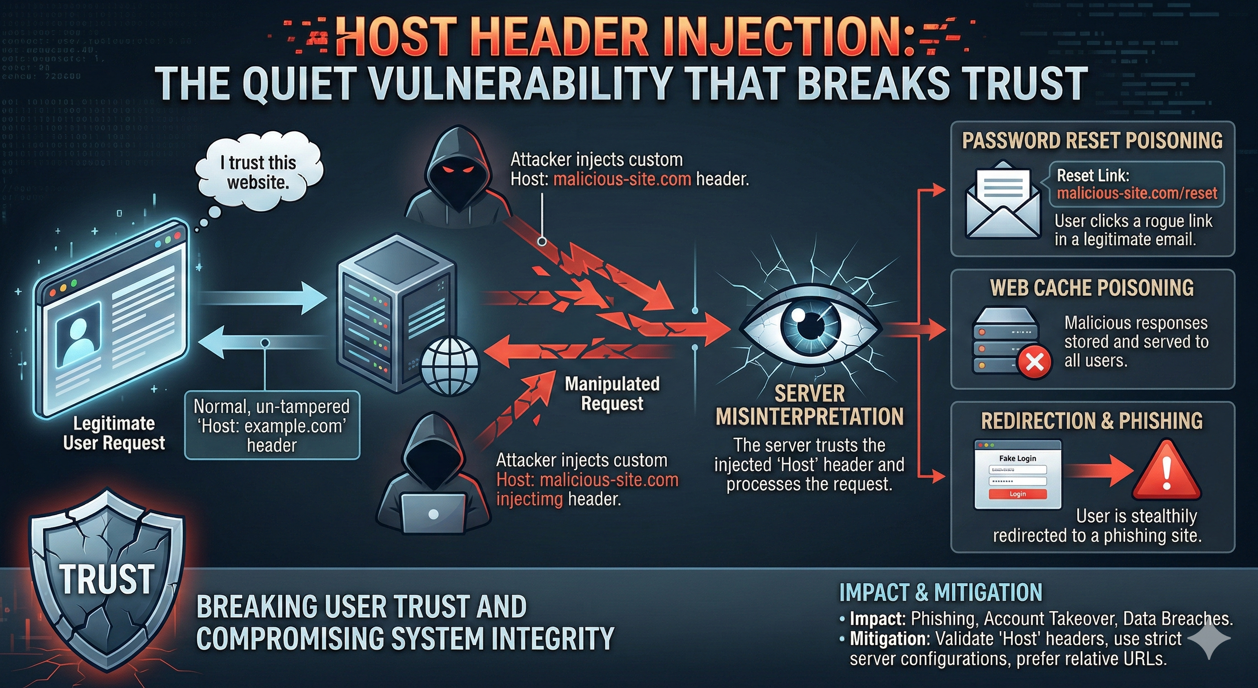
Host header injection is one of those deceptively simple vulnerabilities that can quietly undermine password reset flows, poison caches, bypass authentication logic, and even lead to full account takeover.
Let’s walk through how this works and why it matters more than most teams realize.
What Is the Host Header And Why Does It Matter?
In HTTP/1.1, every request must include a Host header:
GET / HTTP/1.1
Host: example.com
This tells the server which domain the client is trying to access.
On modern infrastructure reverse proxies, load balancers, CDNs this header becomes even more important. It often determines:
Virtual host routing
- Absolute URL generation
- Password reset link construction
- Canonical redirect logic
- Cache keys
- Now imagine:
What if the application trusts this value without validating it?
That’s where problems begin.
Common Host Header Manipulation Techniques
Attackers rarely rely on just one method. Here are several real-world techniques used to manipulate host-based logic.
1. Duplicate Host Headers
Some backend servers and proxies disagree on which Host header to honor.
GET / HTTP/1.1
Host: example.com
Host: hacklido.com
One component may process the first header.
Another may process the second.
Congratulations you now have inconsistent trust boundaries.
2. Whitespace / Parsing Bypass
Sometimes parsers behave unexpectedly when whitespace is introduced:
GET / HTTP/1.1
Host: hacklido.com
Host: example.com
Depending on parsing behavior, the attacker-controlled host may win.
3. Absolute-Form Requests
HTTP allows absolute URLs in request lines:
GET https://example.com/ HTTP/1.1
Host: hacklido.com
If routing logic and application logic disagree, you can create trust confusion between layers.
4. Header Variants
Applications behind proxies often trust forwarded headers:
X-Forwarded-HostX-HTTP-Host-OverrideForwardedX-HostX-Forwarded-Server
If the proxy passes these upstream without strict sanitization, an attacker can override the canonical host value.
5. Port Manipulation
Host: example.com:hacklido.com
Weak parsing logic may split incorrectly and interpret unintended host values.
6. Prefix Confusion
Host: hacklidoexample.com
Improper validation like:
if host.endswith("example.com"):
Can be catastrophically wrong.
7. Subdomain Control
If an attacker controls:
compromised-subdomain.example.com
And the application blindly trusts any*.example.com, the trust boundary collapses.
Exploitation Scenarios
Now let’s move from theory to impact.
1. Password Reset Poisoning
This is one of the most severe outcomes.
Imagine a password reset request:
POST /reset-password HTTP/1.1
Host: example.com
email=victim@example.com
If the application builds the reset link like this:
reset_link = f"https://{request.host}/reset?token=abc"
And the backend trusts X-Forwarded-Host:
X-Forwarded-Host: attacker.com
The victim receives:
https://attacker.com/reset?token=abc
The victim clicks the link.
The token is sent to the attacker-controlled domain.
Account takeover achieved.
No brute force.
No password guessing.
Just trust abuse.
2. Cache Poisoning → Stored XSS
Consider this HTML response:
<script src="https://example.com/wave.js"></script>
Now imagine the server constructs that URL dynamically from Host.
You send:
Host: hacklido.com
The server responds:
<script src="https://hacklido.com/wave.js"></script>
If the response is cached (X-Cache-Status: HIT), every future visitor receives your injected script reference.
You host malicious JavaScript.
Boom stored XSS via cache poisoning.
This is particularly dangerous when:
- CDN cache keys do not include Host
- Reverse proxy caches before validation
- Cache invalidation logic is weak
3. Authentication Bypass via Host-Based Logic
Some systems restrict admin panels like this:
if request.host == "admin.example.com":
allow_access()
Now ask yourself:
What if Host is attacker controlled?
If routing doesn’t enforce strict SNI + host matching at the infrastructure layer, privilege boundaries can collapse.
This becomes especially dangerous in:
- Multi-tenant SaaS
- Internal admin panels
- Staging environments
- Microservice architectures
Why This Vulnerability Persists
You might wonder:
Why do experienced teams still get this wrong?
Because the trust chain is complex:
Browser → CDN → Load Balancer → Reverse Proxy → Application
Each layer may:
- Normalize headers differently
- Merge duplicate headers differently
- Trust forwarded headers incorrectly
- Cache responses based on inconsistent keys
Host header injection is rarely a single bug.
It’s usually a trust boundary failure across layers.
Defensive Measures (What Secure Systems Do)
If you’re building or reviewing infrastructure, here’s what must be enforced:
✔ Strict Host Allowlist
Reject requests unless Host matches an explicit allowed list.
✔ Normalize at the Edge
- CDN or reverse proxy should:
- Drop duplicate Host headers
- Strip untrusted forwarding headers
- Enforce canonical host
✔ Do Not Trust X-Forwarded-Host Blindly
Only accept forwarded headers from trusted internal proxies.
✔ Hardcode Canonical URLs for Sensitive Flows
Password reset links should use configured base URLs not dynamic request data.
✔ Cache Key Hardening
Ensure cache keys include:
- Host
- Protocol
- Relevant headers
Why Security Researchers Love This Bug
Host header injection is elegant.
It doesn’t rely on:
- Memory corruption
- Race conditions
- Exotic protocol abuse
It relies on logic confusion.
And logic bugs are the most dangerous class of vulnerabilities because:
They survive patch cycles.
They pass static analysis.
They hide in configuration.
And when combined with caching or password flows they become critical.
A Question for You
- When was the last time you:
- Tested duplicate Host headers?
- Sent conflicting X-Forwarded-Host values?
- Inspected how your CDN constructs cache keys?
- Reviewed how your password reset URL is generated?
If the answer is “never,” you now have something worth checking.
Final Thoughts
Host header injection isn’t flashy.
But it’s powerful.
It turns infrastructure assumptions into exploit primitives.
It turns misconfiguration into account takeover.
It turns caching into persistent XSS.
And the scariest part?
It often hides in plain sight.
The next time you test a web app, don’t just look at parameters.
Look at the headers.
Sometimes, that’s where trust quietly breaks.
If This Helped You
If this post saved you time, brainpower, or frustration,
feel free to buy me a coffee ☕
Not because you have to.
Just because late-night recon runs better on caffeine.
👉 https://buymeacoffee.com/purushotham
Blog by Purushotham.R
Security Researcher