Hello guys, Vedavyasan here👽✨.
Recently I got several HoF (HALL OF FAME) for reporting a sinlge bug on their several domains through their Nokia vulnerability disclosure program.So that simple bug is called “clickjacking aka ui redressing”.SO let’s get started and please dont forget to clap✨😁😂.
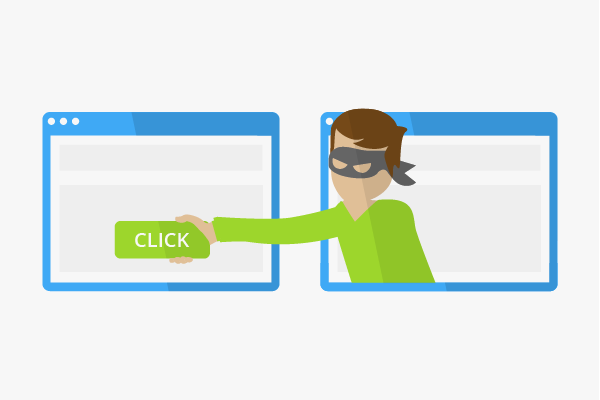
What is clickjacking or ui redressing?
Clickjacking, also known as a “UI redress attack”, is when an attacker uses multiple transparent or opaque layers to trick a user into clicking on a button or link on another page when they were intending to click on the top level page. Thus, the attacker is “hijacking” clicks meant for their page and routing them to another page, most likely owned by another application, domain, or both.
Using a similar technique, keystrokes can also be hijacked. With a carefully crafted combination of stylesheets, iframes, and text boxes, a user can be led to believe they are typing in the password to their email or bank account, but are instead typing into an invisible frame controlled by the attacker.
Examples
For example, imagine an attacker who builds a web site that has a button on it that says “click here for a free iPod”. However, on top of that web page, the attacker has loaded an iframe with your mail account, and lined up exactly the “delete all messages” button directly on top of the “free iPod” button. The victim tries to click on the “free iPod” button but instead actually clicked on the invisible “delete all messages” button. In essence, the attacker has “hijacked” the user’s click, hence the name “Clickjacking”.
###How to find clickjacking attack ?
By Manual method
<html>
<head>
<title>Clickjacking POC</title>
</head>
<body>
<p>Website is vulnerable to clickjacking</p>
<iframe src=”http://example.website.nokia.com” width=”500″ height=”500″>
</iframe>
</body>
</html>
Save this as .html file and open it in browser.
If the targeted site is loaded successfully then it is vulnerable to clickjacking attack.
Method 2:
Visit the URL https://securityheaders.com/ and paste the target and click go.
If the X-Frame-Options header is shows in red colour then it is vulnerable to clickjacking. If it shows in green colour it is not vulnerable to clickjacking.
Method 3:
Visit https://clickjacker.io and paste the target URL. If the page loads successfully, it is vulnerable to clickjacking.
Method 4:
Step1: Check the network tab and reload the site.
Step2: Now visit the target url and check for X-Frame-Options header.
Step3: If the X-Frame-Options header was same origin then it is not vulnerable to clickjacking.
Here for example the site “flipkart.com” has a X-Frame-Options header in its response and it is same origin, so it is not vulnerable to clickjacking attacks. But incase of “testphp.vulnweb.com” it doesn’t has X-Frame-Options header in response so it is vulnerable to clickjacking attacks.
Method 5:
To increase the severity we will use burpsuite.
Step1: Click burp → burp clickbandit → copy clickbandit to clipboard. Once we copied, then go to target site and click inspect element and go to console tab. Paste it and click enter and press start. If the page loads successfully it is vulnerable to clickjacking.
Step2: Click the input fields and click finish to check if the field is vulnerable.
Click the “click” button till it says You’ve been clickjacked!.
Impact
With a crafted combination of stylesheets, iframes, and text boxes, a user can be led to believe they are typing in the password to their email or bank account, but are instead typing into an invisible frame controlled by the attacker.
Profile links:
https://www.instagram.com/ved4vyasan/
https://www.linkedin.com/in/vedavyasan-s-a9825b228/
https://twitter.com/ved4_vyasan