A critical Privilege Escalation vulnerability was identified in the user management functionality where an Admin user can archive (deactivate/delete) a Super Admin account by manipulating the user ID in the request.
This issue occurs due to missing server-side authorization checks, allowing lower-privileged users to perform actions reserved only for top-level administrators.
As a result, an attacker with Admin access can remove the highest authority from the platform, causing serious governance and operational disruption.
Step-by-Step Reproduction
Step 1 — Login
Login using a valid Admin account.
Step 2 — Intercept Request
Navigate to the User Management panel and attempt to archive any normal user.
Intercept the request using an interception proxy such as Burp Suite.
Step 3 — Modify Target ID
Replace the user ID parameter with the Super Admin ID:
/admin/users/superadmin-id
Step 4 — Forward Request
Send the modified request to the server.
Step 5 — Observe
The Super Admin account gets archived successfully, which should never be permitted for an Admin-level user.
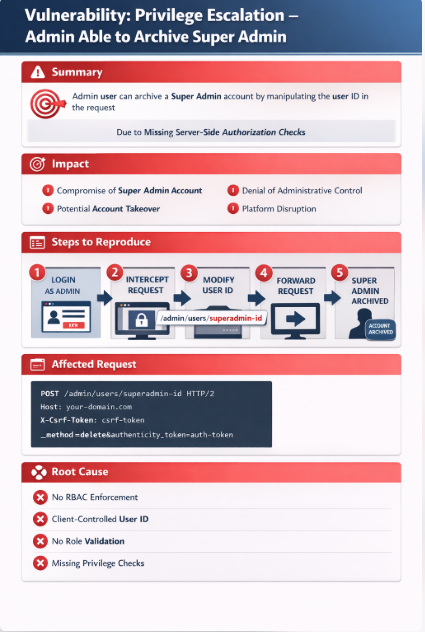
Affected Request
POST /admin/users/superadmin-id HTTP/2
Host: your-domain.cloud.com
Cookie: session-cookie
User-Agent: Mozilla/5.0
Accept: text/html
Referer: https://111.cloud.com/admin/users/
X-Csrf-Token: csrf-token
Content-Type: application/x-www-form-urlencoded
_method=delete&authenticity_token=auth-token
Impact
This vulnerability can severely compromise platform integrity and administrative control:
- Complete compromise of Super Admin account integrity
-
- Potential account takeover scenarios
-
- Denial of administrative control
-
- Platform governance can be disrupted
-
- Risk of malicious insider abuse
-
- Full system configuration may become inaccessible
If exploited in production environments, this flaw could allow attackers to remove key administrative oversight, leading to security chaos.