In the world of modern web development, APIs are the glue holding everything together.
But as we shift toward agentic AI and microservices, APIs have become the #1 target for attackers. If you’re a developer or a bug bounty hunter, understanding the OWASP API Security Top 10 isn’t just a “good-to-know” thing, it’s your survival guide.
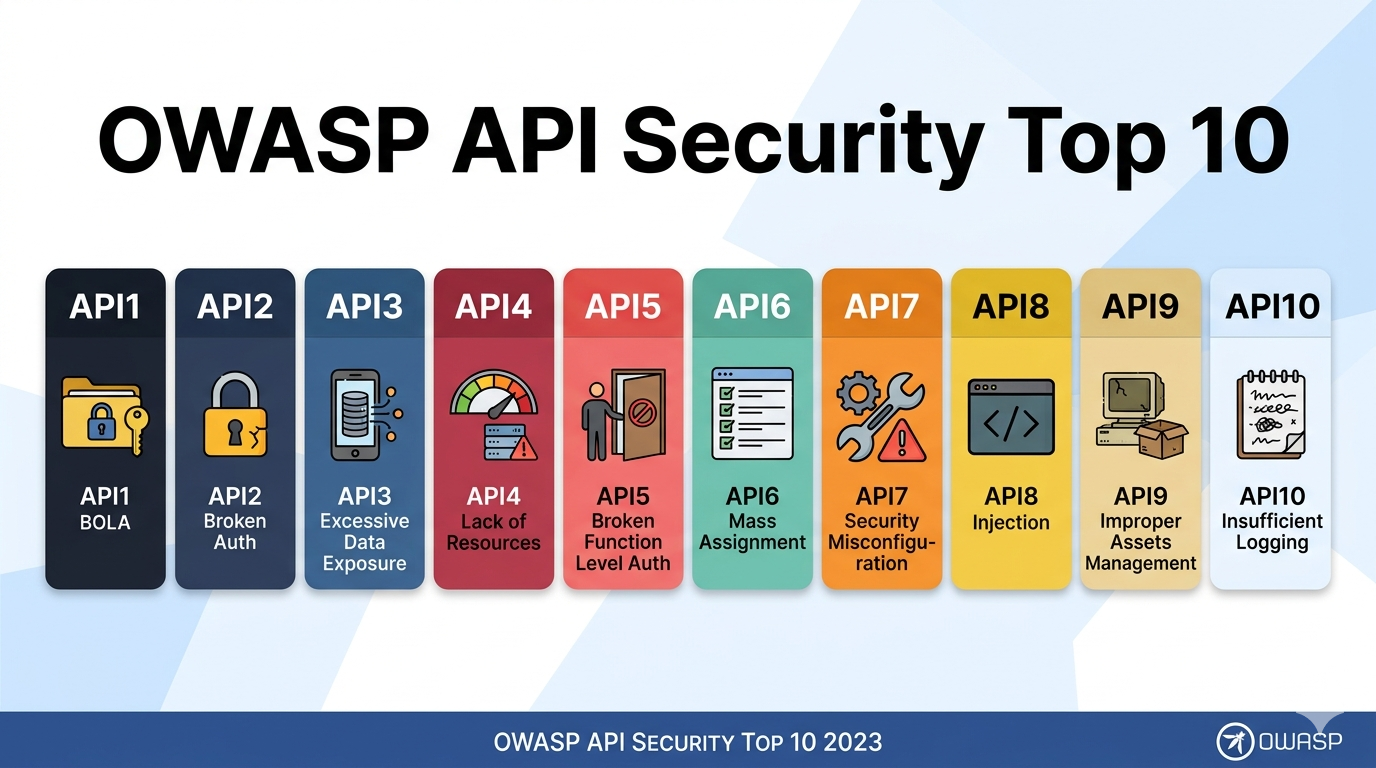
Today we will be diving into OWASP API Security Top 10 Security Risks
1. Broken Object Level Authorization (BOLA)
This is the most common and dangerous API vulnerability.
It happens when an API does not properly check whether a user is allowed to access a specific object.
Example
Imagine this API request:
GET /api/users/102If an attacker changes the ID:
GET /api/users/103And the server returns another user’s data, the API has a Broken Object Level Authorization vulnerability.
Impact
- Attackers can:
- Access other users’ private data
- Modify resources
- Delete sensitive records
2. Broken Authentication
Broken authentication occurs when APIs fail to properly verify user identity.
Common causes
- Weak tokens
- Token leakage
- Improper session management
- No token expiration
Example
If an API accepts an expired token or predictable token, attackers may impersonate legitimate users.
3. Broken Object Property Level Authorization
This vulnerability happens when an API exposes or allows modification of sensitive object properties.
Example
A user updates their profile:
PATCH /api/user
{
“username”: “john”,
“isAdmin”: true
}
If the server does not filter this property, the user may escalate privileges.
4. Unrestricted Resource Consumption
APIs can be abused to consume excessive resources like:
- CPU
- Memory
- Bandwidth
- Database queries
Example
An attacker repeatedly calls an endpoint:
GET /api/search?q=test
Thousands of times per second.
Impact
- This can lead to Denial of Service (DoS) attacks.
5. Broken Function Level Authorization
This occurs when users access API functions they should not be allowed to use.
Example
Normal user endpoint:
GET /api/profile
Admin endpoint:
DELETE /api/users/200If a normal user can call the admin endpoint, it becomes a Broken Function Level Authorization vulnerability.
6. Unrestricted Access to Sensitive Business Flows
Some APIs allow attackers to abuse business logic by automating workflows.
Example
An attacker scripts thousands of requests to:
- Book limited products
- Redeem coupons
- Generate OTPs
Impact
- Inventory abuse
- Financial losses
- Service disruption
7. Server Side Request Forgery (SSRF)
SSRF occurs when an API fetches a remote resource based on user-controlled input.
Example
POST /api/fetch
{
"url":"http://example.com"
}
An attacker may change it to:
http://localhost/admin
or
http://169.254.169.254
This allows access to internal systems or cloud metadata.
8. Security Misconfiguration
Misconfigured APIs can expose sensitive information.
Examples
- Debug mode enabled
- Verbose error messages
- Open cloud storage
- Unnecessary HTTP methods enabled
9. Improper Inventory Management
Organizations often forget about old or undocumented APIs.
Attackers love these because they may:
- Use outdated security
- Expose sensitive data
- Bypass modern protections
10. Unsafe Consumption of APIs
Applications often trust third-party APIs too much.
If external APIs return malicious or unexpected data, it may cause:
- Injection attacks
- Data leaks
- Application crashes
Connect with me in linkedin
https://www.linkedin.com/in/chitra-karanam-417999237/