Although the title seems irrelevant for a cybersecurity blog, it encapsulates the two roles that characterize the digital battlefield.
Red and blue teaming in cybersecurity stand for attackers and defenders, respectively. Let’s examine how deception and investigative abilities function in cybersecurity fields.
**_
The Trump Card of Hackers: Social Engineering
_**
We are all aware that hackers target systems in order to accomplish their objectives, whether they are part of a mission or a personal agenda. But how do they even begin? is the true question. And no, it’s not at all like the dramatic typing and green scrolling code you see in movies.
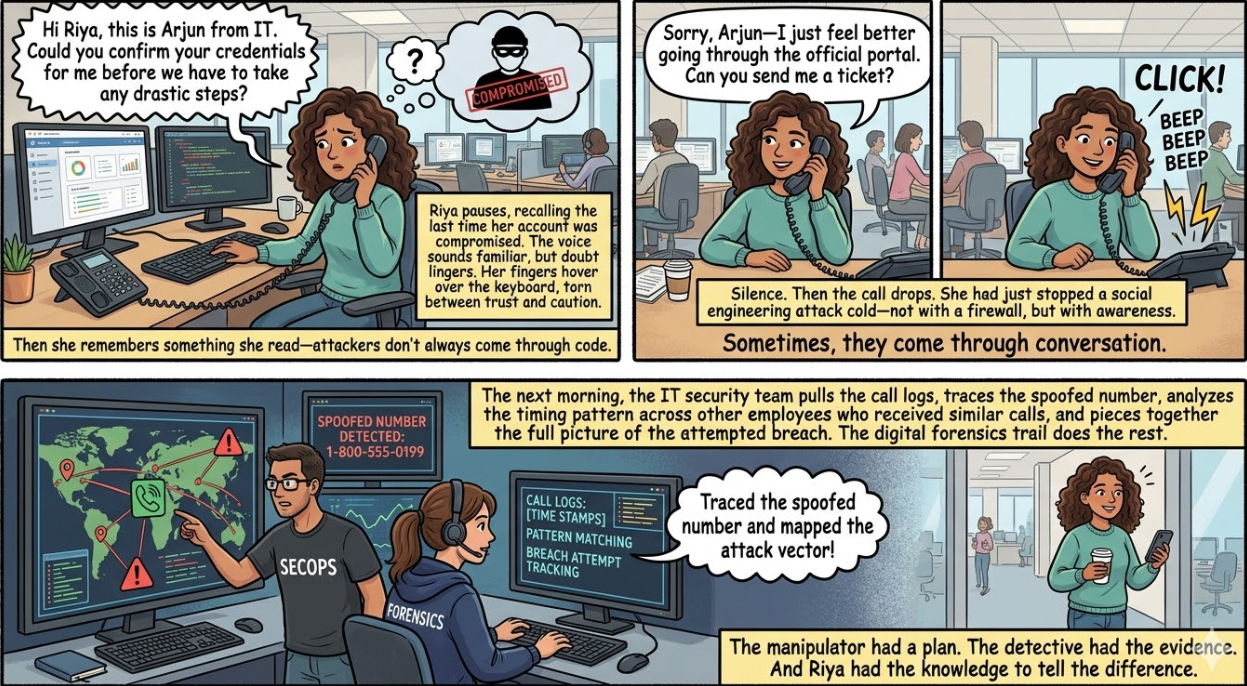
Although hackers use a wide range of methods, strategies, and resources, their most effective tool is surprisingly human: Social engineering is a sophisticated type of “psychological manipulation” that breaches security systems by taking advantage of “human emotions and trust.” This entails using psychological manipulation to compromise security, frequently by taking advantage of people’s feelings and trust.
What precisely is social engineering, then? In short, it is the use of psychology to coerce individuals into voluntarily disclosing private information or taking actions that will help the attacker. The hacker penetrates you rather than firewalls and encryption.
You may now be thinking, “I’m not foolish enough to hand over my data to a hacker.” However, take a look at these actual situations.
- .Deepfakes and Impersonation: A hacker can pose as your boss, a close friend, or a member of your family by using AI-generated audio or video. They call you in an emergency, requesting a quick money transfer or sensitive information. The voice sounds authentic. It seems like a real situation. And you’ve complied before you know it.
- Phishing emails: You get an email that appears to be from Google, your bank, or even the IT department of your business. The language, the formatting, and the logo were all flawlessly duplicated. You give the attacker access to your account in that instant after clicking the link and entering your login information.
Numerous reports and case studies show that these situations are common, impacting thousands of people every day, including tech-savvy professionals. Social engineering frequently gets around technical defenses by taking advantage of psychological weaknesses and human trust.
_
Digital Forensics: The Cybersecurity Detective
_
Now that an attack has happened, who comes in to make sense of the mess? This is where Digital Forensics comes in.
Digital forensics is like Sherlock Holmes for the world of cybersecurity. Just like a detective looks for fingerprints, footprints, and other clues at a crime scene, a digital forensics expert looks through systems, logs, network traffic, and deleted files to figure out what happened.
They have to answer three very important questions:
- What made the attack happen?
- What caused it?
- How was it done?
For example, picture a business getting up one morning to find that private client information has been leaked.
A digital forensics investigator would :
- Check email logs to see if the breach was caused by a phishing attack.
- Look at login records and timestamps to find places where people shouldn’t have been able to get in.
- Get back deleted files or wiped data to find out what was taken and when.
- Use IP addresses and device fingerprints to find out where the attacker came from.
- By putting all of these digital breadcrumbs together, forensic experts can not only find out what was stolen, but they can also find out who planned the attack, even if they tried hard to hide their tracks.
_**
**_
Digital forensics and social engineering are two sides of the same coin. One is the art of manipulation, which means using psychology to carry out an attack. The other is the science of investigation, which means using logic, data, and hard work to find the truth.
A good cybersecurity professional needs to know both social engineering and digital forensics, which connect attack and defense strategies. You need to know how people are tricked and how attacks are tracked to get a full picture of the cyber world, whether you’re building defenses, responding to incidents, or just trying to stay safe online.
Let’s look at a real-life example that shows how important it is to be aware and do research in cybersecurity.