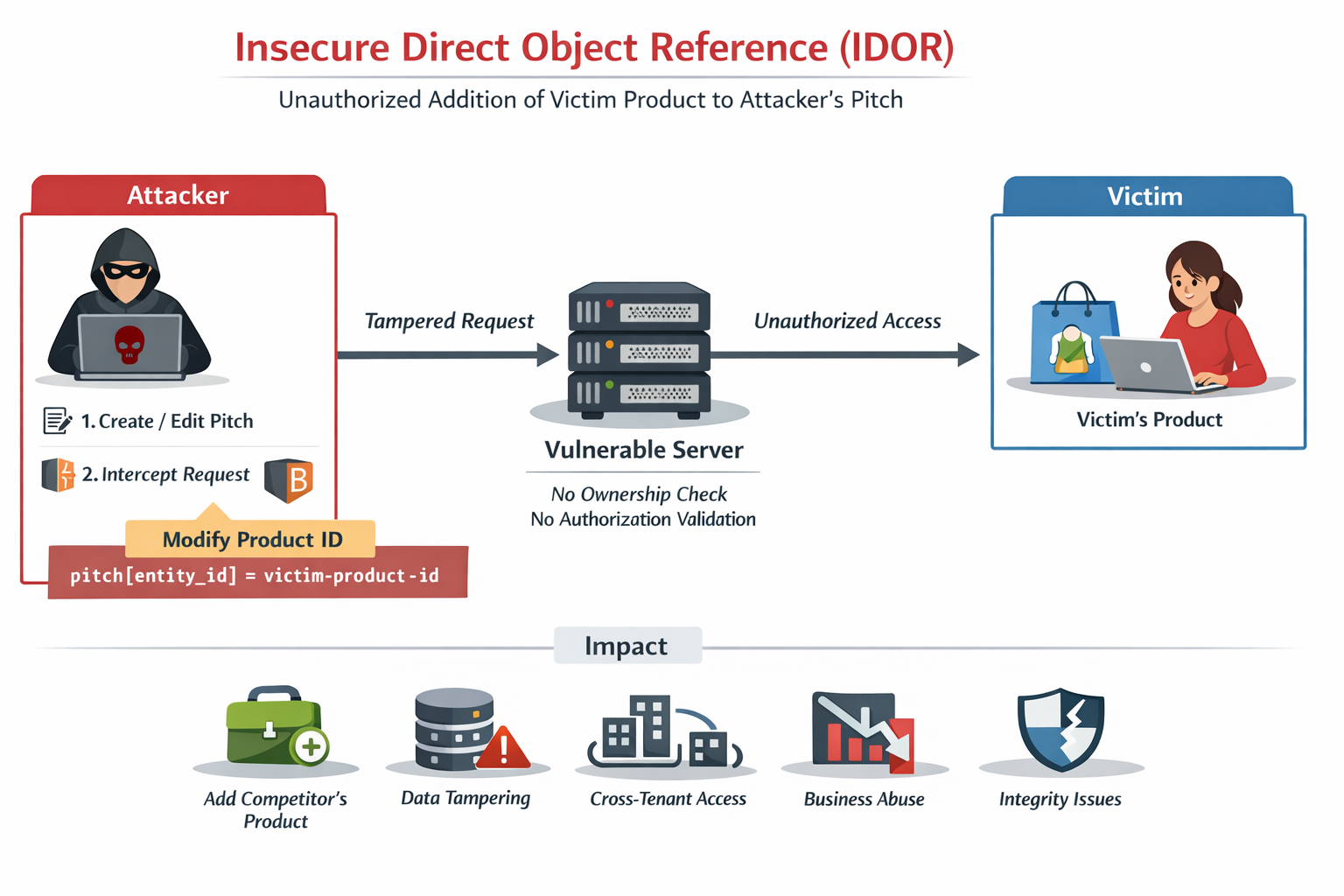
A Broken Access Control vulnerability exists in the pitch management functionality of the Qwoted platform.
The application allows authenticated users to associate products with their pitch, but the backend fails to validate ownership of the product identifier supplied in the request.
By modifying the entity_id parameter inside the request, an attacker can add a victim’s product to their own pitch, even if they do not own or have permission to access that product.
This vulnerability occurs because the backend trusts client-supplied identifiers without verifying authorization, leading to a classic Insecure Direct Object Reference (IDOR).
The vulnerability occurs due to missing server-side authorization validation on the following parameter:
pitch[pitched_entities][][entity_id]
The backend system:
❌ Does not validate product ownership
❌ Does not verify access permissions
❌ Directly links the provided product ID to the pitch
This allows attackers to manipulate object references belonging to other users.
Step-by-Step Reproduction
Step 1 — Login
Login to the application using a normal user account (attacker account).
Step 2 — Intercept Request
While creating or editing a pitch, intercept the request using Burp Suite.
Step 3 — Modify Product ID
Locate the following parameter in the request:
pitch[pitched_entities][][entity_id]
Replace the attacker’s product ID with a victim’s product ID.
Example:
pitch[pitched_entities][][entity_id]=victim-product-id
Step 4 — Send the Request
Forward the modified request to the server.
Step 5 — Observe the Result
The server accepts the request and adds the victim’s product to the attacker’s pitch, even though the attacker does not own the product.
Affected Request
PUT /api/internal/pitches/1680530 HTTP/2
Host: app.com
Content-Type: multipart/form-data
Cookie: session-cookie
X-Csrf-Token: csrf-token
——boundary
Content-Disposition: form-data; name=“pitch[pitched_entities][][entity_id]”
victim-product-id
——boundary
Content-Disposition: form-data; name=“pitch[pitched_entities][][entity_type]”
Product
——boundary–
Impact
An attacker can exploit this vulnerability to:
• Add victim products to their pitch
• Manipulate other users’ resources
• Tamper with cross-tenant data
• Abuse competitor assets
• Break multi-tenant isolation
• Cause data integrity issues