
Network Devices
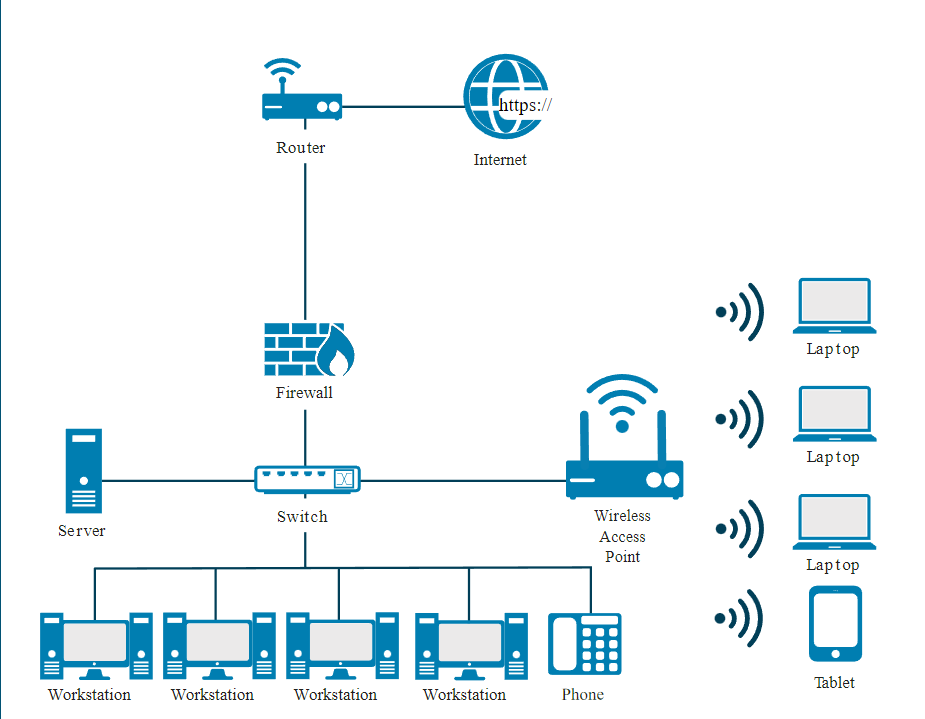
- Hubs are used to connect multiple devices in a network. They’re less likely to be seen in business or corporate networks than in home networks. Hubs are wired devices and are not as smart as switches or routers.
- Switches are wired devices that know the addresses of the devices connected to them and route traffic to that port/device rather than retransmitting to all devices.
- Switches can also create separate broadcast domains when used to create VLANs, which will be discussed later.
- Routers are used to control traffic flow on networks and are often used to connect similar networks and control traffic flow between them.
- Routers can be wired or wireless and can connect multiple switches.
- Smarter than hubs and switches, routers determine the most efficient “route” for the traffic to flow across the network.
- Firewalls are essential tools in managing and controlling network traffic and protecting the network.
- A firewall is a network device used to filter traffic.
- It is typically deployed between a private network and the internet,
- but it can also be deployed between departments (segmented networks) within an organization (overall network).
- Firewalls filter traffic based on a defined set of rules, also called filters or access control lists.
- Server is a computer that provides information to other computers on a network.
- Some common servers are web servers, email servers, print servers, database servers and file servers.
- All of these are, by design, networked and accessed in some way by a client computer.
- Servers are usually secured differently than workstations to protect the information they contain.
- Endpoints are the ends of a network communication link.
- One end is often at a server where a resource resides, and the other end is often a client making a request to use a network resource.
- An endpoint can be another server, desktop workstation, laptop, tablet, mobile phone or any other end user device.
Device Address
Media Access Control (MAC) Address:
- Every network device is assigned a Media Access Control (MAC) address. An example is
00-13-02-1F-58-F5.
- The first 3 bytes (24 bits) of the address denote the vendor or manufacturer of the physical network interface.
- No two devices can have the same MAC address in the same local network; otherwise an address conflict occurs.
Internet Protocol (IP) Address:
- While MAC addresses are generally assigned in the firmware of the interface, IP hosts associate that address with a unique logical address.
- This logical IP address represents the network interface within the network and can be useful to maintain communications when a physical device is swapped with new hardware.
- Examples are
192.168.1.1 and 2001:db8::ffff:0:1.
Rules to compress IP addresses are
Rule 1: When there are continuous zeros (0s) in the IPv6 address notation, they are replaced with :: This rule is also known as zero compression.
For example,
Original IPv6 = ef82:0000:0000:0000:0000:1a12:1234:1b12
Compressed IPv6 = ef82::1a12:1234:1b12
Rule 2: Leading zeros (0s) in the 16 bits field can be removed (right side). But each block in which you do this, have at least one number remaining. If the field contains all zeros (0s), you have to leave one zero (0) remaining.
Removing leading zeros (0s) does not have any effect on the value. However, you cannot apply this rule to trailing zeros (0s). This rule is also known as leading zero compression.
For example,
Original IPv6 = 1234:0fd2:5621:0001:0089:0000:0000:4500
Compressed IPv6 = 1234:fd2:5621:1:89:0:0:4500
Rule 3: When zeros (0s) are present in discontinuous pattern in IPv6 address notation, then at only one junction, the zeros (0s) are replaced with ::.
For example,
Original IPv6 = 2001:1234:0000:0000:1b12:0000:0000:1a13
Compressed
IPv6 = 2001:1234::1b12:0:0:1a13
or
IPv6 = 2001:1234:0:0:1b12::1a13
Ports & Protocols
Physical ports:
- Are the ports on the routers, switches, servers, computers, etc. that you connect the wires,
- E.g., fiber optic cables, Cat5 cables, etc., to create a network.
Logical port
- Also called a socket - is little more than an address number that both ends of the communication link agree to use when transferring data.
- Ports allow a single IP address to be able to support multiple simultaneous communications, each using a different port number.
- In the Application Layer of the TCP/IP model (which includes the Session, Presentation, and Application Layers of the OSI model) reside numerous application - or service-specific protocols.
Types of logical ports
- Well-known ports (0–1023): Commons ports.
- These ports are related to the common protocols that are at the core of the TCP/IP model, DNS, SMTP, etc.
- Registered ports (1024–49151): Vendor specific ports.
- These ports are often associated with proprietary applications from vendors and developers.
- While they are officially approved by the Internet Assigned Numbers Authority (IANA), in practice many vendors simply implement a port of their choosing.
- Examples include Remote Authentication Dial-In User Service (RADIUS) authentication (1812), Microsoft SQL Server (1433/1434) and the Docker REST API (2375/2376).
- Dynamic or private ports (49152–65535): Service specific random ports.
- Whenever a service is requested that is associated with well-known or registered ports,
- those services will respond with a dynamic port that is used for that session and then released.
Protocols
- Data types are mapped using port numbers associated with services. For example, web traffic (or HTTP) is port 80.
- Secure web traffic (or HTTPS) is port 443.
- You’ll note that in several cases a service (or protocol) may have two ports assigned, one secure and one insecure.
- When in doubt, systems should be implemented using the most secure version as possible of a protocol and its services.
FTP
- Port 21, File Transfer Protocol (FTP) sends the username and password using plaintext from the client to the server.
- This could be intercepted by an attacker and later used to retrieve confidential information from the server.
- The secure alternative, SFTP, on port 22 uses encryption to protect the user credentials and packets of data being transferred.
Telnet
- Port 23, telnet, is used by many Linux systems and any other systems as a basic text-based terminal.
- All information to and from the host on a telnet connection is sent in plaintext and can be intercepted by an attacker.
- This includes username and password as well as all information that is being presented on the screen, since this interface is all text.
- Secure Shell (SSH) on port 22 uses encryption to ensure that traffic between the host and terminal is not sent in a plaintext format.
SMPT
- Port 25, Simple Mail Transfer Protocol (SMTP) is the default unencrypted port for sending email messages.
- Since it is unencrypted, data contained within the emails could be discovered by network sniffing.
- The secure alternative is to use port 587 for SMTP using Transport Layer Security (TLS) which will encrypt the data between the mail client and the mail server.
Time
- Port 37, Time Protocol, may be in use by legacy equipment and has mostly been replaced by using port 123 for Network Time Protocol (NTP).
- NTP on port 123 offers better error-handling capabilities, which reduces the likelihood of unexpected errors.
DNS
- Port 53, Domain Name Service (DNS), is still used widely.
- However, using DNS over TLS (DoT) on port 853 protects DNS information from being modified in transit.
HTTP
- Port 80, HyperText Transfer Protocol (HTTP) is the basis of nearly all web browser traffic on the internet.
- Information sent via HTTP is not encrypted and is susceptible to sniffing attacks.
- HTTPS using TLS encryption is preferred, as it protects the data in transit between the server and the browser.
- Note that this is often notated as SSL/TLS.
- Secure Sockets Layer (SSL) has been compromised is no longer considered secure.
- It is now recommended for web servers and clients to use Transport Layer Security (TLS) 1.3 or higher for the best protection.
IMAP
- Port 143, Internet Message Access Protocol (IMAP) is a protocol used for retrieving emails.
- IMAP traffic on port 143 is not encrypted and susceptible to network sniffing.
- The secure alternative is to use port 993 for IMAP, which adds SSL/TLS security to encrypt the data between the mail client and the mail server.
SNMP
- Ports 161 and 162, Simple Network Management Protocol, are commonly used to send and receive data used for managing infrastructure devices.
- Because sensitive information is often included in these messages, it is recommended to use SNMP version 2 or 3 (abbreviated SNMPv2 or SNMPv3) to include encryption and additional security features.
- Unlike many others discussed here, all versions of SNMP use the same ports, so there is not a definitive secure and insecure pairing.
- Additional context will be needed to determine if information on ports 161 and 162 is secured or not.
SMB
- Port 445, Server Message Block (SMB), is used by many versions of Windows for accessing files over the network.
- Files are transmitted unencrypted, and many vulnerabilities are well-known. Therefore, it is recommended that traffic on port 445 should not be allowed to pass through a firewall at the network perimeter.
- A more secure alternative is port 2049, Network File System (NFS). Although NFS can use encryption, it is recommended that NFS not be allowed through firewalls either.
LDAP
- Port 389, Lightweight Directory Access Protocol (LDAP), is used to communicate directory information from servers to clients.
- This can be an address book for email or usernames for logins.
- The LDAP protocol also allows records in the directory to be updated, introducing additional risk.
- Since LDAP is not encrypted, it is susceptible to sniffing and manipulation attacks.
- Lightweight Directory Access Protocol Secure (LDAPS) adds SSL/TLS security to protect the information while it is in transit on port 636 - LDAPS.
Types of threats
Spoofing
- An attack with the goal of gaining access to a target system through the use of a falsified identity.
- Spoofing can be used against IP addresses, MAC address, usernames, system names, wireless network SSIDs, email addresses, and many other types of logical identification.
Phishing
- An attack that attempts to misdirect legitimate users to malicious websites through the abuse of URLs or hyperlinks in emails could be considered phishing.
DOS/DDOS
- A denial-of-service (DoS) attack is a network resource consumption attack that has the primary goal of preventing legitimate activity on a victimized system.
- Attacks involving numerous unsuspecting secondary victim systems are known as distributed denial-of-service (DDoS) attacks.
Virus
- The computer virus is perhaps the earliest form of malicious code to plague security administrators.
- As with biological viruses, computer viruses have two main functions -> propagation and destruction.
- A virus is a self-replicating piece of code that spreads without the consent of a user, but frequently with their assistance (a user has to click on a link or open a file).
Worm
- Worms pose a significant risk to network security.
- They contain the same destructive potential as other malicious code objects with an added twist -> they propagate themselves without requiring any human intervention.
Trojan
- Named after the ancient story of the Trojan horse, the Trojan is a software program that appears benevolent but carries a malicious, behind-the-scenes payload that has the potential to wreak havoc on a system or network.
- For example, ransomware often uses a Trojan to infect a target machine and then uses encryption technology to encrypt documents, spreadsheets and other files stored on the system with a key known only to the malware creator.
On-path Attack
- In an on-path attack, attackers place themselves between two devices, often between a web browser and a web server, to intercept or modify information that is intended for one or both of the endpoints.
- On-path attacks are also known as man-in-the-middle (MITM) attacks.
Side-channel
- A side-channel attack is a passive, noninvasive attack to observe the operation of a device.
- Methods include power monitoring, timing and fault analysis attacks.
Advanced Persistent Threat (APT)
- Advanced persistent threat (APT) refers to threats that demonstrate an unusually high level of technical and operational sophistication spanning months or even years.
- APT attacks are often conducted by highly organized groups of attackers.
Insider Threat
- Threats that arise from individuals who are trusted by the organization.
- These could be disgruntled employees or employees involved in espionage.
- Insider threats are not always willing participants.
- A trusted user who falls victim to a scam could be an unwilling insider threat.
- [[Part 1 - Describe the concepts of security, compliance, and identity]]
Malware
- A program that is inserted into a system, usually covertly, with the intent of compromising the confidentiality, integrity or availability of the victim’s data, applications or operating system or otherwise annoying or disrupting the victim.
Ransomware
- Malware used for the purpose of facilitating a ransom attack.
- Ransomware attacks often use cryptography to “lock” the files on an affected computer and require the payment of a ransom fee in return for the “unlock” code.
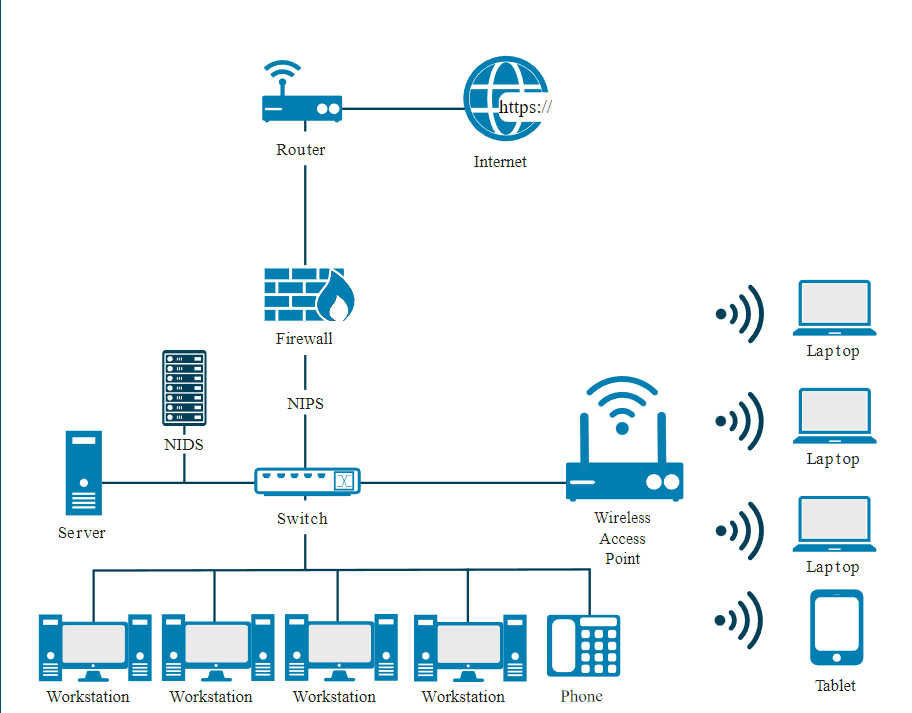
Intrusion Detection System (IDS)
- Automates the inspection of logs and real-time system events to detect intrusion attempts and system failures.
- An IDS is intended as part of a defense-in-depth security plan.
- It will work with, and complement, other security mechanisms such as firewalls, but it does not replace them.
- HIDS: Host Based Intrusion Detection Systems - Monitors a single computer or host.
- NIDS: Network Based Intrusion Detection Systems - Moniters a network by traffic patterns.
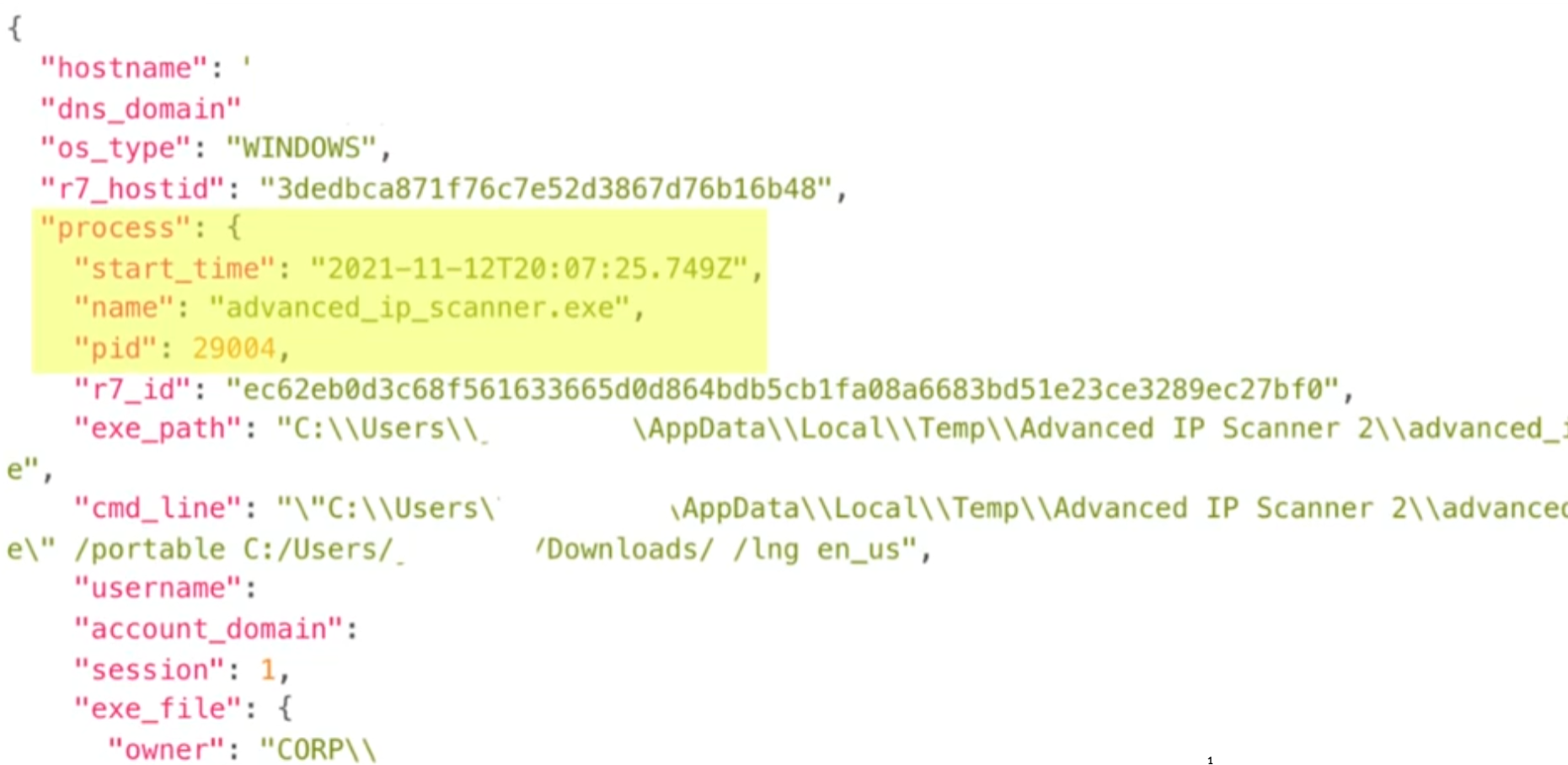
- The
pid or Process ID indicates when the application was executed, like if it’s very lower it means it started along with the boot sequence else was started much later.
Preventing Threats
- Keep systems and applications up to date.
- Remove or disable unneeded services and protocols.
- Use intrusion detection and prevention systems.
- Use up-to-date anti-malware software.
- Antivirus - usage is strongly encouraged as a security best practice and is a requirement for compliance with the Payment Card Industry Data Security Standard (PCI DSS).
- Use firewalls.
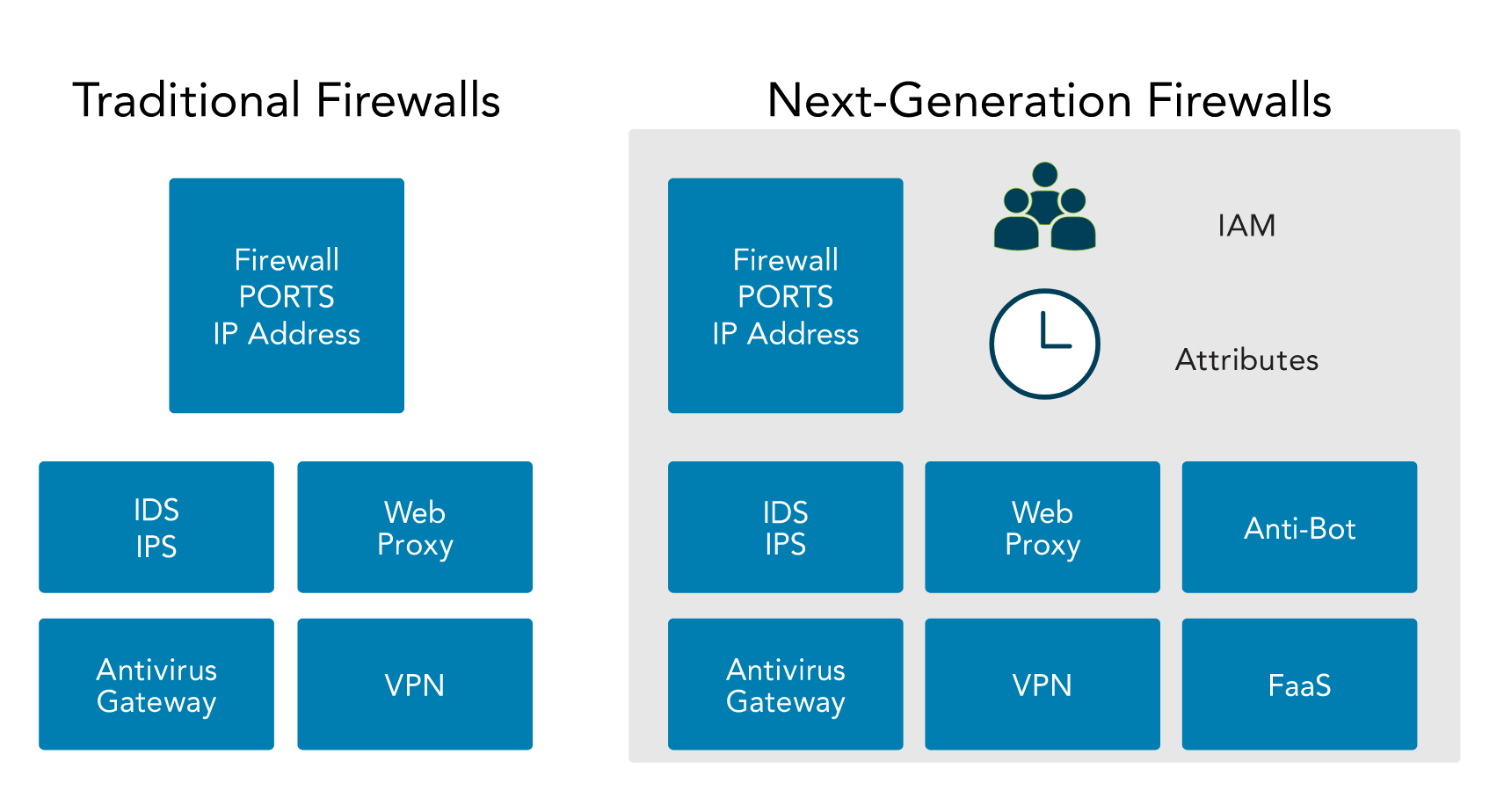
Intrusion Prevention System (IPS)
- An intrusion prevention system (IPS) is a special type of active IDS that automatically attempts to detect and block attacks before they reach target systems.
- A distinguishing difference between an IDS and an IPS is that the IPS is placed in line with the traffic.
- In other words, all traffic must pass through the IPS and the IPS can choose what traffic to forward and what traffic to block after analyzing it.
- This allows the IPS to prevent an attack from reaching a target.
- Since IPS systems are most effective at preventing network-based attacks, it is common to see the IPS function integrated into firewalls. Just like IDS, there are Network-based IPS (NIPS) and Host-based IPS (HIPS).
- IDS
Select (Identify/Prevent/Both) - Identify. An Intrusion Detection System helps to identify threats, but does not have the capability to prevent them.
—
- HIDS
Select (Identify/Prevent/Both) - Identify. A Host Intrusion Detection System helps to identify threats to a host system, but does not prevent them.
—
- NIDS
Select (Identify/Prevent/Both) - Identify. A Network Intrusion Detection System helps to identify threats based on network traffic, but does not prevent them.
—
- SIEM
Select (Identify/Prevent/Both) - Identify. A Security Incident and Event Management system identifies threats by correlating and storing logs from multiple systems, but does not take action to prevent the threats from materializing.
—
- Anti-malware/Antivirus
Select (Identify/Prevent/Both) - Both. Anti-malware/Antivirus helps to both identify and prevent threats by identifying malicious software and stopping the processes before they fully execute.
—
- Scans
Select (Identify/Prevent/Both) - Identify. Scans help to identify threats, often by conducting a vulnerability analysis, and may suggest action to mitigate the threats, but does not prevent them.
—
- Firewall
Select (Identify/Prevent/Both) - Both. Most modern firewalls both identify and prevent threats by automatically adjusting rules to block malicious traffic from entering a secured network.
—
- IPS (NIPS/HIPS)
Select (Identify/Prevent/Both) - Both. Intrusion Prevention Systems both identify and prevent threats.
- - -
Heating, Ventilation and Air Conditioning (HVAC) Environment
- High-density equipment and equipment within enclosed spaces requires adequate cooling and airflow.
- Well-established standards for the operation of computer equipment exist, and equipment is tested against these standards.
- For example, the recommended range for optimized maximum uptime and hardware life is from 64° to 81°F (18° to 27°C), and it is recommended that a rack have three temperature sensors, positioned at the top, middle and bottom of the rack, to measure the actual operating temperature of the environment.
- Proper management of data center temperatures, including cooling, is essential.
- Cooling is not the only issue with airflow: Contaminants like dust and noxious fumes require appropriate controls to minimize their impact on equipment.
- Monitoring for water or gas leaks, sewer overflow or HVAC failure should be integrated into the building control environment, with appropriate alarms to signal to organizational staff.
- Contingency planning to respond to the warnings should prioritize the systems in the building, so the impact of a major system failure on people, operations or other infrastructure can be minimized.

Redundancy
- The concept of redundancy is to design systems with duplicate components so that if a failure were to occur, there would be a backup.
- This can apply to the data center as well.
- Risk assessments pertaining to the data center should identify when multiple separate utility service entrances are necessary for redundant communication channels and/or mechanisms.
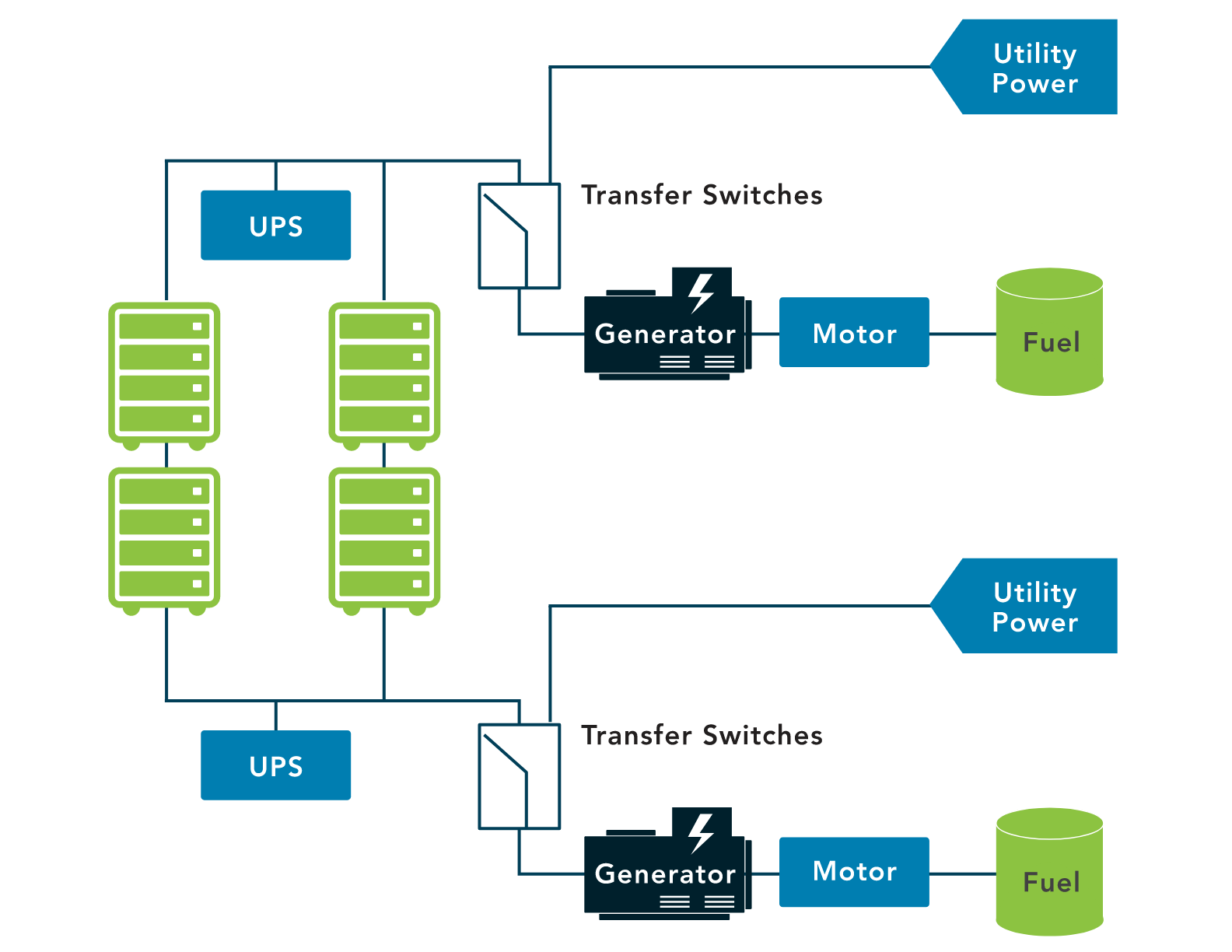
- If the organization requires full redundancy, devices should have two power supplies connected to diverse power sources.
- Those power sources would be backed up by batteries and generators.
- In a high-availability environment, even generators would be redundant and fed by different fuel types.
- UPS - Uninterupted Power Supply
Memorandum of Understanding (MOU)/Memorandum of Agreement (MOA)
- Some organizations seeking to minimize downtime and enhance BC (Business Continuity) and DR (Disaster Recovery) capabilities will create agreements with other, similar organizations.
- They agree that if one of the parties experiences an emergency and cannot operate within their own facility, the other party will share its resources and let them operate within theirs in order to maintain critical functions.
- These agreements often even include competitors, because their facilities and resources meet the needs of their particular industry.
Hospital A and Hospital B are competitors in the same city. The hospitals create an agreement with each other: if something bad happens to Hospital A (a fire, flood, bomb threat, loss of power, etc.), that hospital can temporarily send personnel and systems to work inside Hospital B in order to stay in business during the interruption (and Hospital B can relocate to Hospital A, if Hospital B has a similar problem). The hospitals have decided that they are not going to compete based on safety and security—they are going to compete on service, price and customer loyalty. This way, they protect themselves and the healthcare industry as a whole.
- These agreements are called joint operating agreements (JOA) or memoranda of understanding (MOU) or memoranda of agreement (MOA).
- Sometimes these agreements are mandated by regulatory requirements, or they might just be part of the administrative safeguards instituted by an entity within the guidelines of its industry.
SLA
- The cloud computing service-level agreement (cloud SLA) is an agreement between a cloud service provider and a cloud service customer based on a taxonomy of cloud computing– specific terms to set the quality of the cloud services delivered.
- The minimum level of service, availability, security, controls, processes, communications, support and many other crucial business elements are stated and agreed to by both parties
- The service level agreement goes down to the granular level.
- For example, if I’m outsourcing the IT services, then I will need to have two full-time technicians readily available, at least from Monday through Friday from eight to five.
- With cloud computing, I need to have access to the information in my backup systems within 10 minutes.
- An SLA specifies the more intricate aspects of the services.
The difference between an MOA or MOU and an SLA: is that a Memorandum of Understanding is more directly related to what can be done with a system or the information.
- We must be very cautious when outsourcing with cloud-based services, because we have to make sure that we understand exactly what we are agreeing to.
- If the SLA promises 100 percent accessibility to information, is the access directly to you at the moment, or is it access to their website or through their portal when they open on Monday?
- That’s where you’ll rely on your legal team, who can supervise and review the conditions carefully before you sign the dotted line at the bottom.
“Cloud” by NIST Definition -
“a model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (such as networks, servers, storage, applications, and services) that can be rapidly provisioned and released with minimal management effort or service provider interaction.” NIST SP 800-145
More about cloud infrastructure, service models, deployement models [[Part 1 - Describe the concepts of security, compliance, and identity]]
Network Design
The objective of network design is to satisfy data communication requirements and result in efficient overall performance.
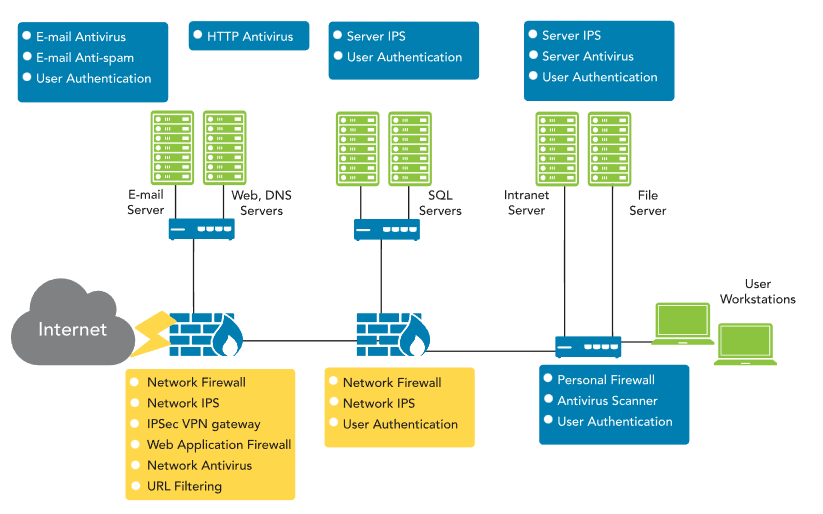
Network segmentation
- Involves controlling traffic among networked devices.
- Complete or physical network segmentation occurs when a network is isolated from all outside communications,
- so transactions can only occur between devices within the segmented network.
Demilitarized Zone
- A DMZ is a network area that is designed to be accessed by outside visitors but is still isolated from the private network of the organization.
- The DMZ is often the host of public web, email, file and other resource servers.
Virtual Local Area Network
- VLANs are created by switches to logically segment a network without altering its physical topology.
Virtual Private Network
- A virtual private network (VPN) is a communication tunnel that provides point-to-point transmission of both authentication and data traffic over an untrusted network.
Network Access Control (NAC)
- Network access control (NAC) is a concept of controlling access to an environment through strict adherence to and implementation of security policy.
Defence in depth, Zero Trust - Reference: [[Part 1 - Describe the concepts of security, compliance, and identity]]
Network Access Policy
- The goal is to ensure that all devices wishing to join the network do so only when they comply with the requirements laid out in the organization policies.
- This visibility will encompass internal users as well as any temporary users such as guests or contractors, etc., and any devices they may bring with them into the organization.
Microsegmentation
- Extreme granular restrictions with complex controls (Logical Rules).
- The toolsets of current adversaries are polymorphic in nature and allow threats to bypass static security controls.
- Modern cyberattacks take advantage of traditional security models to move easily between systems within a data center.
- Microsegmentation aids in protecting against these threats.
- A fundamental design requirement of microsegmentation is to understand the protection requirements for traffic within a data center and traffic to and from the internet traffic flows.
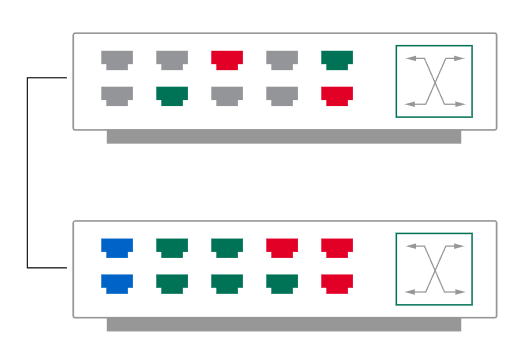
VLAN
- Virtual local area networks (VLANs) allow network administrators to use switches to create software-based LAN segments within,
- and decide whether the VLAN can communicate with each or not,
- which can segregate or consolidate traffic across multiple switch ports.
VPN
- A virtual private network (VPN) is not necessarily an encrypted tunnel.
- It is simply a point-to-point connection between two hosts that allows them to communicate.
- Secure communications can, of course, be provided by the VPN, but only if the security protocols have been selected and correctly configured to provide a trusted path over an untrusted network, such as the internet.
- Remote users employ VPNs to access their organization’s network, and depending on the VPN’s implementation, they may have most of the same resources available to them as if they were physically at the office.
- As an alternative to expensive dedicated point-to-point connections, organizations use gateway-to-gateway VPNs to securely transmit information over the internet between sites or even with business partners.