
Hello folks I hope you are doing well. I’m a Parag Bagul security Researcher and bug bounty hunter.
This article is based on a 2022 finding in which I discovered the Backup file leak vulnerability on Oracle website which leads to sensitive information disclosure.
THE FINDING:
While i was exploring this website i found some subdomains
- subdomain enumeration:
subfinder -d oracle.com -o domain.txt
2.Extracting Live Subdomains using HTTPX
cat domain.txt |httpx > active.txt
3.Uncovering Hidden Backup Files:
I found the domain ‘labs.oracle.com’ in the active domains list.
Sometimes, developers save backup files with the subdomain name included, such as ‘test.example.com/test.zip’.
Same scenario in my case After open labs.oracle.com/lab.zip in a browser I found that it was leaking sensitive information .sql files.
labs.oracle.com/lab.zip
So the final tip is Always check every combination Backup files like:
test.example.com/test.zip
test.example.com/example.zip
test.example.com/test.example.zip
Also check different file extension like zip,7z,tar,gz,bz2,xz
test.example.com/test.rar
test.example.com/test.7z
test.example.com/test.tar
test.example.com/test.gz
test.example.com/test.bz2
test.example.com/test.xz
Also check common format of Common names that developers use for a website source code backup in a ZIP file format you can also fuzz them.
sourcecode.zip
website_source.zip
website_backup.zip
website-source-code.zip
source.zip
backup.zip
code.zip
website-code.zip
website_code_backup.zip
source-code-backup.zip
website-files.zip
website-folder.zip
source-code.zip
code-backup.zip
website-code-backup.zip
website-src.zip
website-src-code.zip
website-src-backup.zip
src-code.zip
website-data-backup.zip
Also you can automate this kinds of things with burpsuite intruder,nuclei.
Report status:
Report date: 08-AUG-2022
Patch date: 09-AUG-2022
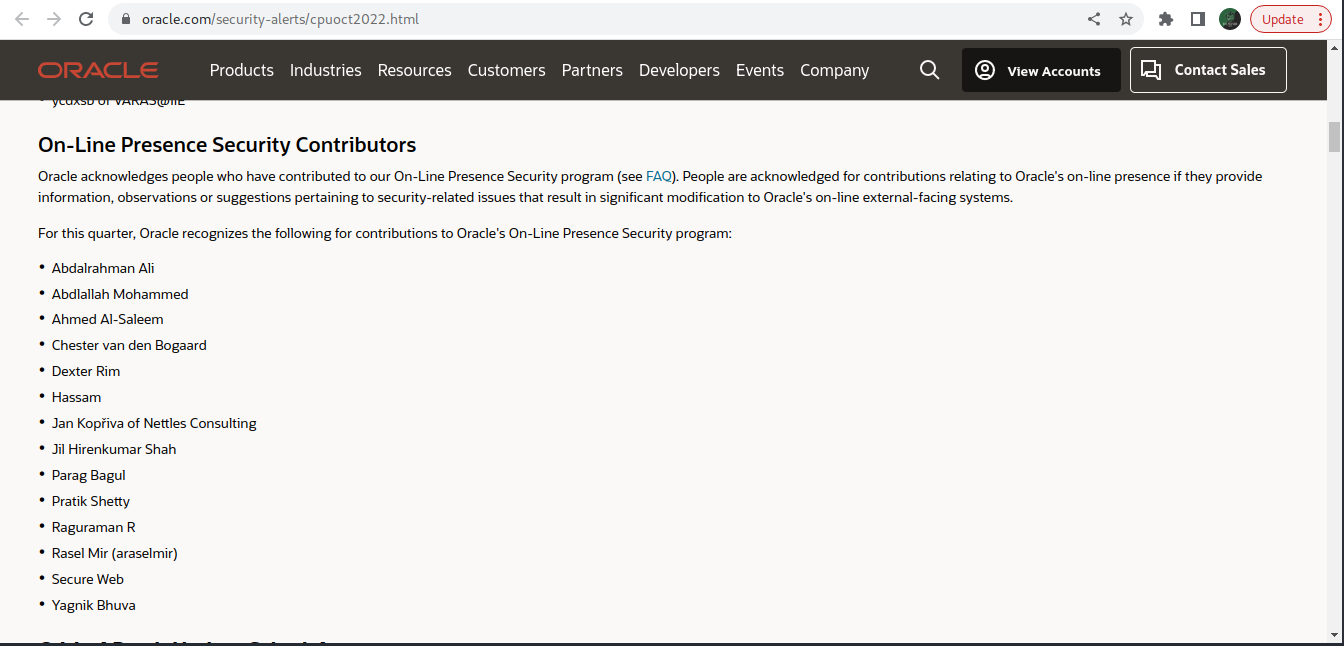
Added in Hall of fame : 18-OCT-2022
Thank you,
Parag Bagul!!
HaxWizard
Bug Bounty