I was trying to install termux app on my android 5.1 as I was trying to convert my phone into a remote hacking device by using Kali Net-Hunter. As usual, I started to search for the apk file. I referred to David Bombal’s video and searched for the app in Termux’s Github, but none of the apk files was working as my phone was showing a Parse error. So I searched some other sites out of which one was:-
On the site, I was shown an SHA-256 value which was dc5cb69718f5317d87ccc3dced11729cd2656f87f308481b84896b53d19f4e40. After downloading, I verified the value by using HashCalc, which matched the previous one. I thought to search for it on VirusTotal and I found only 1 security vendor’s report to be malicious(https://www.virustotal.com/gui/file/dc5cb69718f5317d87ccc3dced11729cd2656f87f308481b84896b53d19f4e40/detection). I went to the Permissions Section in the Channel’s Tab where I found “android.permission.WRITE_EXTERNAL_STORAGE” which means that the app would be able to write to any files or folders in any attached external device like SD cards.
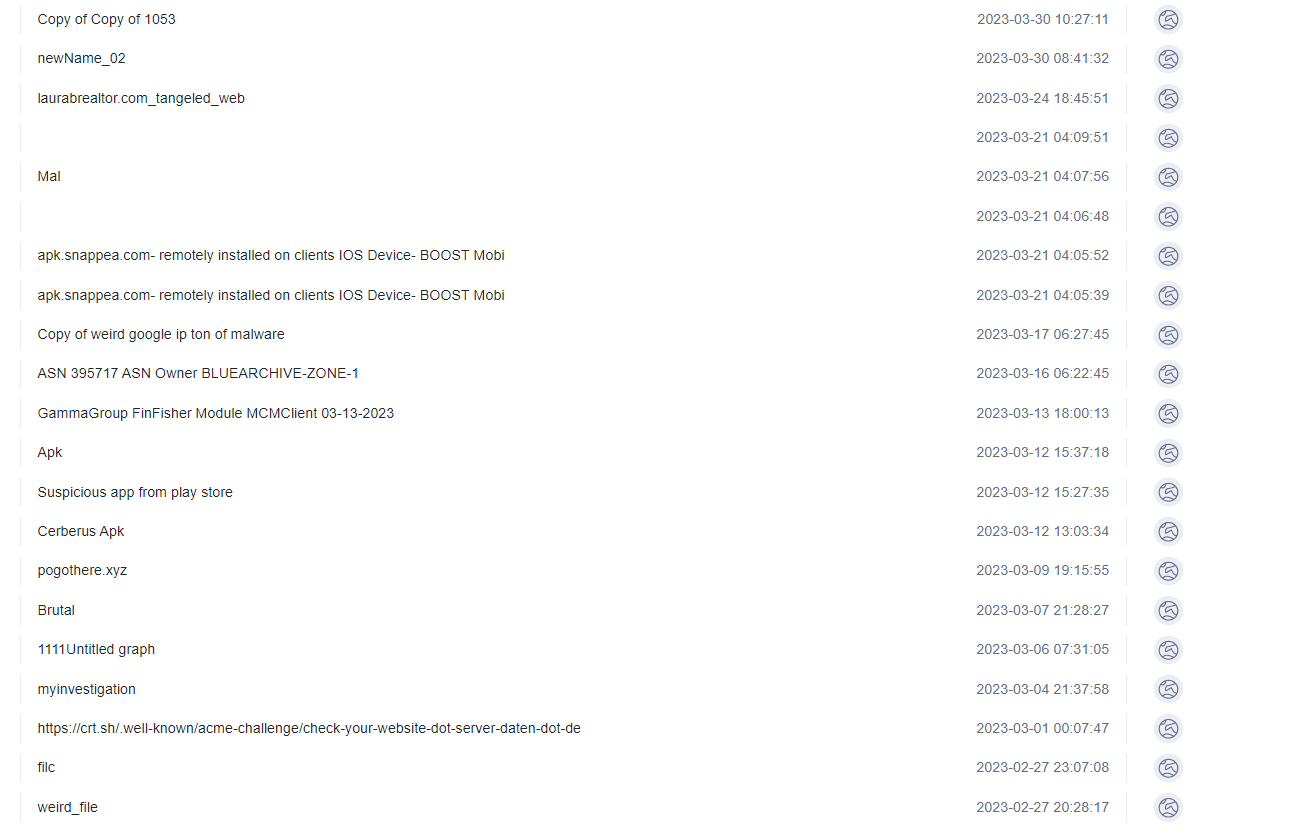
Then I thought to check the IP address contacted with the application. Out of 22 connected addresses 8 were malicious which when searched individually showed reports for Cypher Rats, Whatsapp GB, Spyware Phishing Sophisticated Trackers, malicious excel files, Mobile Ransomware, etc. Link to 8 IPs reports of Virustotal are here below:
- https://www.virustotal.com/gui/ip-address/142.250.178.10
- https://www.virustotal.com/gui/ip-address/142.250.179.234
- https://www.virustotal.com/gui/ip-address/142.250.180.10
- https://www.virustotal.com/gui/ip-address/142.250.180.14
- https://www.virustotal.com/gui/ip-address/142.250.187.202
- https://www.virustotal.com/gui/ip-address/142.250.200.10
- https://www.virustotal.com/gui/ip-address/142.250.200.42
- https://www.virustotal.com/gui/ip-address/142.250.200.238
You can go ahead and explore the VT graphs associated or use the Mobsf tool to understand the dynamic analysis of the application. Remember, If you think technology can solve your security problems, then you don’t understand the problems and you don’t understand the technology. Until next time!