This GitHub repo is made for all, ranging from beginners in cybersecurity to cybersecurity experts. This is beginner-friendly, so don’t worry and enjoy reading.
Introduction to Nmap
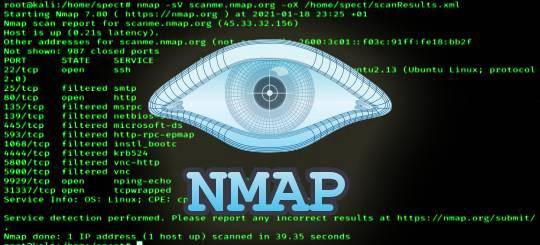
Nmap, short for Network Mapper, is an open-source tool that is used to scan IP addresses and ports of a machine or on a network.
Nmap can be used for the following purposes -
- creating a complete network Map
- detecting open ports on local and remote systems
- getting os system and software details
- finding vulnerabilities on local and remote hosts
- detecting installed applications on a host
Now let’s understand about different commands of Nmap.
Ping Command –used to test the reachability of a host on the Internet (Checking whether the system is online or not).
For example -
or
Scan Command — used to find open and closed ports and the service running on that port on local and remote systems
Note -
Add -v after nmap if you want to view the details while the scan is running or wait for the scan to complete.
If you want to change the DNS service the Nmap is using to find IP addresses by domain name, then use the below command.
nmap –dns-servers 1.1.1.1 mywebsite.com
If you want to scan for a range of ports, then use the following command:
nmap -p1–30 mywebsite.com
If you want to scan for a particular port, then use the following command:
Version Detection Command — used for remote os Detection
Aggressive Scan Command — used to enable OS detection, version detection, script scanning, and traceroute (Just insert -A in the command)
Note –
For identifying live hosts on a local network, use the following command:
nmap.exe -sP defaultgateway/24
For finding all live hosts on a local network, just simply enter netdiscover in a kali Linux terminal.
For scanning for multiple ports of your choice, use the following command:
nmap -p80,443,23 mywebsite.com
Now let’s see some cool examples of Nmap -
To scan for port 80 on all local addresses run:
nmap -p80 192.168.7.1/24 -v
To scan port 80 on localhost run:
or
To scan multiple ports on one host run:
nmap -p80,443,2000,4444 google.com
To scan a range of ports from 1 to 100 or any given range, run:
To scan for all available ports run:
To scan for specific service, HTTP for example run:
or
To scan for all http-related services run:
or
To scan for HTTPS service run:
To scan for all https-related services run:
Nmap Scripting Engine(NSE)
The Nmap Scripting Engine (NSE) is one of Nmap’s most powerful and flexible features. It allows users to write (and share) simple scripts (using the Lua programming language ) to automate a wide variety of networking tasks. Those scripts are executed in parallel with the speed and efficiency you expect from Nmap.
To begin with, nse scripts run this example:
nmap -sV — script http-title scanme.nmap.org
to include multiple nse scripts in one scan:
nmap -sV — script http-title,http-headers scanme.nmap.org
to run all the scripts in NSE vulnerability category run:
nmap — script vuln scanme.nmap.org
to run all the scripts from multiple NSE categories run:
nmap -sV — script=”version,discovery” scanme.nmap.org
to run all the scripts from exploit category run:
nmap -sV — script exploit scanme.nmap.org
to exclude specific nse category (in this case exploit category) run:
nmap -sV — script “not exploit: scanme.nmap.org
to exclude specific nse scripts (in this example we are excluding http-slowloris and http-brute) from nse category run:
nmap -sV — script “(http-*) and not (http-slowloris or http-brute)” scanme.nmap.org
DNS Bruteforce Command — used to bruteforce dns record
nmap –script dns-brute google.com
OS Identification Command — To find the details of OS
nmap -O scanme.nmap.org -v
FAQ
What are alternatives to Nmap?
There are a number of alternatives available on GitHub today, but still, Nmap is the most popular and widely used. Some of the famous ones are
https://github.com/angryip/ipscan https://github.com/robertdavidgraham/masscan
Is Nmap available in GUI?
Zenmap is the gui version of Nmap. Windows users can install that for ease of use.
https://nmap.org/zenmap/
For suggestions, feel free to create a pull request on the github repo and I will update that in the blog too.tps://nmap.org/zenmap/
https://github.com/dheerajydv19/A-Beginner-s-Guide-to-Nmap
You can follow me for learning my writeups on topics related to ethical hacking and cybersecurity and a few topics on technology and to knowing my tips and tricks which I use to save my time and for better results.
https://linktr.ee/dheerajydv19