Exploring the Working Principle, Exploitation Techniques, and Prevention Measures of Broken Authentication in OWASP API2 | Karthikeyan Nagaraj
Introduction:
- Authentication is a critical component of web application security, as it helps to ensure that only authorized users can access sensitive data and resources.
- However, if authentication mechanisms are poorly implemented or managed, they can be vulnerable to attack.
- One such vulnerability is Broken Authentication, which is a common flaw in web applications that can allow attackers to gain unauthorized access to user accounts and sensitive data.
- This article aims to provide a comprehensive guide to Broken Authentication in OWASP API2, including its working principle, exploitation techniques, and prevention measures.
Working Principle of Broken Authentication:
Broken Authentication is a vulnerability that occurs when authentication mechanisms are implemented improperly, leading to weaknesses that can be exploited by attackers. Some common causes of Broken Authentication include:
- eak password policies that allow users to choose weak or easily guessable passwords.
- Failure to implement multi-factor authentication, which can provide an additional layer of security.
- Failure to properly manage user sessions, which can allow attackers to hijack active sessions and gain unauthorized access.
- Failure to protect authentication credentials, such as usernames and passwords, from theft or unauthorized access.
How to Exploit Broken Authentication:
Attackers can exploit Broken Authentication vulnerabilities in various ways, including:
- Brute force attacks, where attackers try to guess usernames and passwords using automated tools.
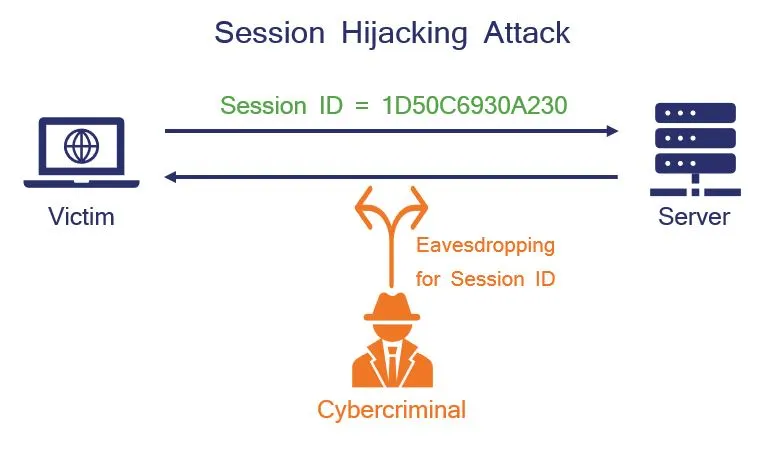
- Session hijacking, where attackers steal session tokens or cookies to gain unauthorized access to user accounts.
- Password spraying, where attackers try a small number of commonly used passwords across multiple accounts to gain unauthorized access.
- Credential stuffing, where attackers use lists of stolen usernames and passwords from other sources to gain unauthorized access to user accounts.
Prevention Measures for Broken Authentication:
To prevent Broken Authentication vulnerabilities, developers and organizations should implement the following measures:
- Implement strong password policies that require users to choose complex, unique passwords.
- Implement multi-factor authentication, which provides an additional layer of security.
- Properly manage user sessions, including using secure session tokens, expiring sessions after a period of inactivity, and preventing session fixation attacks.
- Protect authentication credentials, including using secure protocols such as HTTPS and storing passwords in a hashed and salted format.
- Implement rate limiting and other security measures to prevent brute force attacks and other automated attacks.
Other Considerations for Broken Authentication:
In addition to the above prevention measures, it is also important to consider the following:
- Regularly audit and review authentication mechanisms to identify and fix vulnerabilities.
- Educate users on proper password management and security practices.
- Monitor user activity and behavior to detect and prevent unauthorized access and abuse.
- Stay up-to-date on the latest security threats and vulnerabilities and implement appropriate mitigation measures.
Conclusion:
- Broken Authentication is a serious vulnerability in web applications that can lead to unauthorized access and compromise of sensitive data.
- By understanding the working principle of Broken Authentication and implementing appropriate prevention measures, developers and organizations can protect against this type of attack and ensure the security of their web applications.
- It is essential to regularly review and update security measures to stay ahead of evolving threats and protect against emerging vulnerabilities.