The era of thinking "it's just a style sheet" is officially over. Google has issued an emergency security update for Chrome to address CVE-2026-2441, a high-severity Use-After-Free (UAF) vulnerability that is currently being exploited in the wild. This marks the first confirmed zero-day of 2026 for the world’s most popular browser.
The Technical Breakdown: Memory Corruption via CSS
Most browser exploits target the JavaScript engine (V8), but CVE-2026-2441 resides in the Blink rendering engine, specifically within the CSS font feature values processing logic.
- The Flaw: In C++, the language powering Blink, memory must be managed manually. The bug occurs when Chrome deallocates (frees) a memory object related to CSS font styles but keeps a "dangling pointer" (a reference) to that location.
- The Hijack: An attacker can use a crafted HTML page to "spray" the browser's heap memory. By filling the recently freed space with malicious code, the attacker ensures that when the CSS engine tries to use that dangling pointer, it inadvertently executes the attacker's instructions instead.
- No Interaction Required: This is a "drive by" exploit. A user does not need to download a file or click "Allow"—simply visiting a compromised website or viewing a malicious ad is enough to trigger the code execution within the browser's sandbox.
The "72-Hour Treadmill"
This emergency patch comes just days after a routine security update, highlighting what researchers call the "Zero-Day Treadmill." As soon as one hole is plugged, sophisticated actors—often state-sponsored or initial access brokers pivot to the next undisclosed flaw in their library.
Are You Protected?
The vulnerability affects all Chromium-based browsers, meaning users of Microsoft Edge, Brave, Opera, and Vivaldi are also at risk until their respective vendors push out the upstream fix.
Check your version immediately:
- Windows & macOS: You must be on 145.0.7632.75/76 or newer.
- Linux: You must be on 144.0.7559.75 or newer.
- ChromeOS: The fix is rolling out in version 138.0.7204.305 (LTS).
The Hacklido Takeaway
For the security researchers here, CVE-2026-2441 is a reminder of the inherent risks in memory-unsafe languages like C++.
- Memory Safety is the Future: Interestingly, Firefox is largely immune to this specific class of CSS bug because its rendering engine (Stylo) is written in Rust, which prevents Use-After-Free errors at the compiler level.
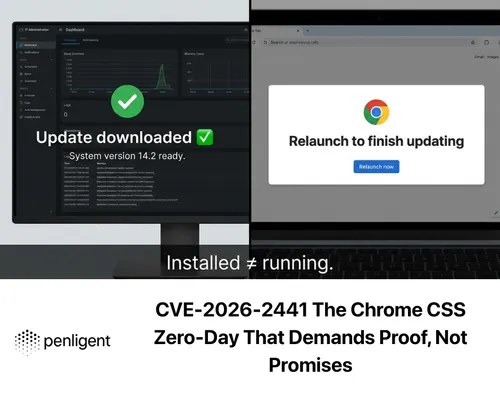
- Relaunch is Key: Chrome often downloads updates in the background, but the patch is not active until you restart the browser. If you see the "Update" bubble in the top-right corner, click it now.
Sandbox Escape Risk: While this exploit currently runs code inside the browser's "sandbox," history shows that attackers often chain these flaws with a second "escape" bug to gain full administrative control of the underlying OS.