The cybersecurity world is witnessing a massive escalation in cyber-extortion activity as a new global threat report reveals a staggering 389% year-over-year increase in ransomware victims. This surge is being driven by the industrialization of cybercrime and the integration of agentic AI tools that allow threat actors to compress their attack lifecycles. At the center of this storm is the notorious group ShinyHunters, which is currently the target of a high-stakes international law enforcement operation following a relentless "pay-or-leak" spree.
1. The 389% Surge: AI and "Shadow Agents"
The Fortinet 2026 Global Threat Landscape Report has sent shockwaves through the industry, documenting a rise from 1,600 confirmed victims in 2025 to over 7,831 in 2026.
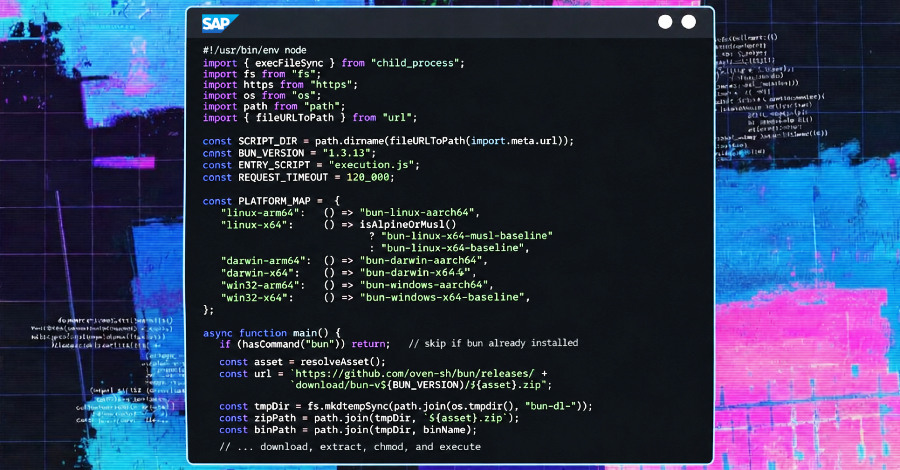
- The AI Catalyst: The availability of crime-service kits like WormGPT, FraudGPT, and BruteForceAI has allowed less-skilled operators to execute sophisticated campaigns.
- Attack Velocity: The window to exploit critical vulnerabilities has shrunk to just 24–48 hours, down from nearly five days in previous years.
- Top Targets: Manufacturing (1,284 victims), business services (824), and retail (682) remain the most heavily hit sectors.
2. ShinyHunters: The "Scattered LAPSUS$ Hunters" Blitz
ShinyHunters, now operating as part of a consolidated "supergroup" known as Scattered LAPSUS$ Hunters (SLH), has launched an aggressive data-theft campaign. This loose alliance combines Scattered Spider’s social engineering expertise with ShinyHunters' automated data-extraction tools.
- Salesforce Exploits: The group reportedly stole data from nearly 400 companies by exploiting misconfigured Salesforce Experience Cloud portals.
- Recent High-Profile Victims:
- Pitney Bowes: 8.2 million records exposed.
- Medtronic: Over 9 million records allegedly stolen.
- Carnival Cruises: Millions of unique customer records leaked.
- Other Targets: The Asian Football Confederation, Udemy, and Rockstar Games have all been named in recent leak cycles.
3. The Global Crackdown
Law enforcement agencies, including the FBI and CISA, have intensified their focus on ShinyHunters' infrastructure. While the group continues to harass executives and "swat" families to force payments, authorities are moving to disrupt the underlying cloud platforms and identity management services the group exploits to hit multiple organizations at once.
Hacklido Intelligence: Survival in the Era of Agentic AI
The shift from encryption-focused ransomware to pure data extortion means that a breach is no longer just a technical failure it is a permanent reputational event.
Strategic Defensive Steps:
- Audit Salesforce Portals: Check for overly permissive "Guest User" configurations on all public-facing Experience Cloud environments.
- Move to FIDO2: The SLH group excels at bypassing standard MFA through vishing. Mandatory hardware security keys are the only reliable defense against their social engineering playbook.
- Monitor UNC Paths: In light of the recent NTLM theft resurgence, monitor your outbound SMB traffic to block credential-harvesting attempts.
- Zero-Trust Identity: Assume your internal credentials are being targeted by automated "Shadow Agents" designed to find and replay stolen session tokens.
The Verdict: In 2026, cybercrime is no longer a collection of isolated hackers; it is an industrialized machine powered by AI. To survive the ShinyHunters blitz, defenders must adopt the same velocity as the threats they face.