LAPSUS$ Resurfaces, Claims Major AstraZeneca Data Breach
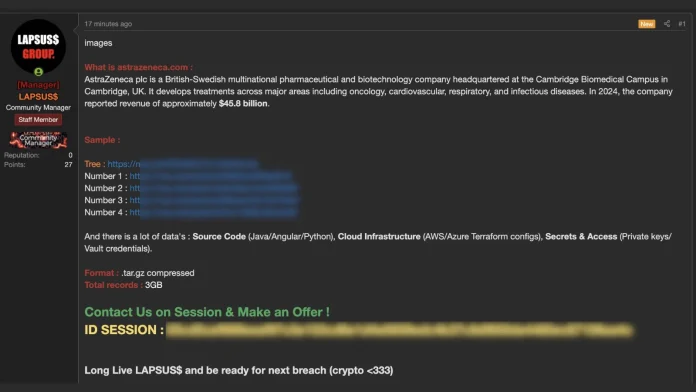
The notorious hacking group LAPSUS$ has allegedly resurfaced, claiming responsibility for a significant data breach involving multinational pharmaceutical and biotechnology company AstraZeneca.
According to reports circulating on cybercrime forums, the threat actors are attempting to sell a compressed 3GB internal data dump, suggesting a possible shift toward pay-to-access extortion tactics rather than immediate public leaks.
Alleged Sale of Stolen Internal Data
LAPSUS$, a group previously linked to high-profile cyberattacks against major technology companies, now appears to be active again with what it claims is a compromise of AstraZeneca’s internal systems.
The group has reportedly posted teaser samples of the stolen data on illicit forums, outlining the contents of a .tar.gz archive and sharing screenshots as proof of access. Rather than releasing the entire dataset publicly, the attackers are allegedly inviting interested buyers to contact them through the secure messaging platform Session to negotiate a sale.
So far, no complete leak has been released for free, which indicates that the group’s primary motive in this case may be financial profit through direct sale.
The threat actors have also shared password-protected paste links containing redacted secrets as additional proof for prospective buyers.
As of March 20, 2026, AstraZeneca has not issued any public comment or official statement regarding the alleged breach.
What the Attackers Claim Was Stolen
According to the claims made on the breach forum, the alleged 3GB data dump contains a wide range of highly sensitive internal assets, including source code, cloud infrastructure files, and access credentials.
Allegedly Compromised Data Includes:
Source Code
- Java Spring Boot applications
- Angular frontend frameworks
- Various Python scripts
Cloud Infrastructure
- Terraform configurations for AWS and Azure environments
- Ansible roles used for automation and orchestration
Secrets and Access
- Private cryptographic keys
- Vault credentials
- Authentication tokens related to GitHub and Jenkins CI/CD pipelines
Exposed Internal Repository Details
To support their claims, the attackers have reportedly released public samples showing internal repository structures and project details.
One exposed directory tree allegedly reveals a root folder named AZU_EXFIL, which contains a key supply-chain portal repository identified as als-sc-portal-internal.
This internal portal appears to be linked to several core pharmaceutical logistics functions, including:
- Forecasting
- Inventory tracking
- Product master data management
- SAP system integration
- On-Time In-Full (OTIF) delivery metrics
Potential Impact
If the breach claims are genuine, the incident could have serious implications for AstraZeneca’s internal operations. The leaked materials may expose not only proprietary source code, but also sensitive cloud infrastructure configurations and access credentials that could increase security risks across its systems.
The possible exposure of supply-chain-related repositories is especially concerning, as it may affect business-critical processes tied to pharmaceutical distribution and logistics.
No Official Confirmation Yet
At this stage, the alleged AstraZeneca breach remains unverified. The claims are based on posts made by threat actors on cybercrime forums, and AstraZeneca has not officially confirmed or denied the incident.
Until the company releases a statement or independent verification emerges, the breach should be treated as an unconfirmed but serious cybersecurity claim.