ComfyUI Servers Targeted in Cryptomining Botnet Campaign
An active cyberattack campaign is targeting internet-exposed instances of ComfyUI, a widely used Stable Diffusion platform, to recruit them into a cryptocurrency mining and proxy botnet.
According to security researcher Mark Ellzey from Censys, attackers are using a custom-built Python scanner to continuously scan cloud IP ranges for vulnerable systems.
How the Attack Works
- The scanner identifies exposed ComfyUI instances.
- It checks for vulnerable custom nodes or installs one via ComfyUI-Manager.
- Exploits a misconfiguration that allows unauthenticated remote code execution (RCE).
- Executes malicious Python payloads through custom nodes.
Targeted Custom Nodes
The attack specifically looks for these node families:
- Vova75Rus/ComfyUI-Shell-Executor
- filliptm/ComfyUI_Fill-Nodes
- seanlynch/srl-nodes
- ruiqutech/ComfyUI-RuiquNodes
If none are found, the attacker installs a malicious node package and retries exploitation.
What Happens After Infection
Once compromised, systems are:
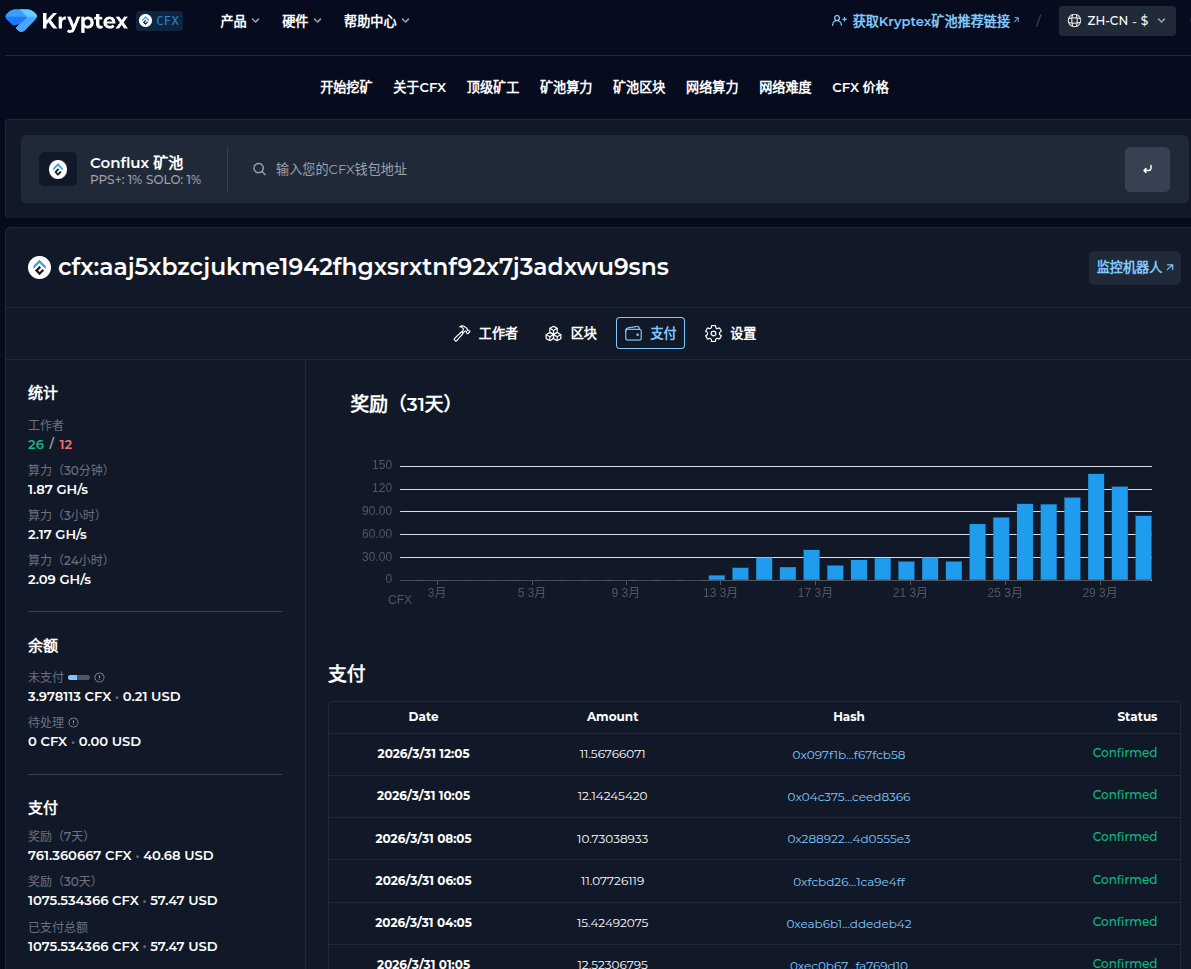
1. Enrolled in Crypto Mining
- Mine Monero using XMRig
- Mine Conflux using lolMiner
2. Added to Proxy Botnet
- Integrated into a Hysteria V2 botnet
- Used as proxy infrastructure for further monetization
3. Controlled Remotely
- Managed through a Flask-based command-and-control (C2) dashboard
Persistence & Evasion Techniques
The malware uses several advanced persistence methods:
- Re-downloads payload every 6 hours
- Re-executes exploit on ComfyUI startup
- Disables shell history
- Kills competing miners
- Uses LD_PRELOAD to hide processes
- Copies itself to multiple locations
- Uses
chattr +ito make files undeletable
It even targets a competing botnet (“Hisana”) by:
- Hijacking its mining configuration
- Redirecting profits to attacker wallets
- Blocking its control port
Scale of Exposure
- Over 1,000 publicly accessible ComfyUI instances identified
- Attack tools discovered on infrastructure linked to Aeza Group (bulletproof hosting provider)
Additional Findings
- Evidence of connections to a Redis-targeting worm campaign
- Tools appear hastily built but effective
- Part of a broader effort to exploit exposed services for profit
Related Botnet Activity Trends
Recent campaigns include:
- Exploiting vulnerabilities in n8n and Tenda routers (Zerobot botnet)
- Attacks on Apache ActiveMQ, Metabase, and React (Kinsing malware)
- Zero-day exploitation in fnOS NAS (NetDragon malware)
- Expansion of RondoDox exploit arsenal
- New Condi malware variant (“QTXBOT”)
- SSH brute-force campaigns deploying miners (Monaco operation)
According to Spamhaus, botnet activity surged significantly in 2025, driven largely by variants of the Mirai botnet.
Key Takeaway
This campaign highlights a critical issue:
Exposed AI tools and developer platforms are becoming prime targets for automated exploitation.
Even relatively small numbers of vulnerable systems can generate significant profits when abused for:
- Cryptomining
- Proxy services
- Botnet expansion